 IPSec遂道配置参数解析.docx
IPSec遂道配置参数解析.docx
- 文档编号:8901995
- 上传时间:2023-02-02
- 格式:DOCX
- 页数:26
- 大小:126.84KB
IPSec遂道配置参数解析.docx
《IPSec遂道配置参数解析.docx》由会员分享,可在线阅读,更多相关《IPSec遂道配置参数解析.docx(26页珍藏版)》请在冰豆网上搜索。
IPSec遂道配置参数解析
FW防火墙配置IPSec遂道参数解析
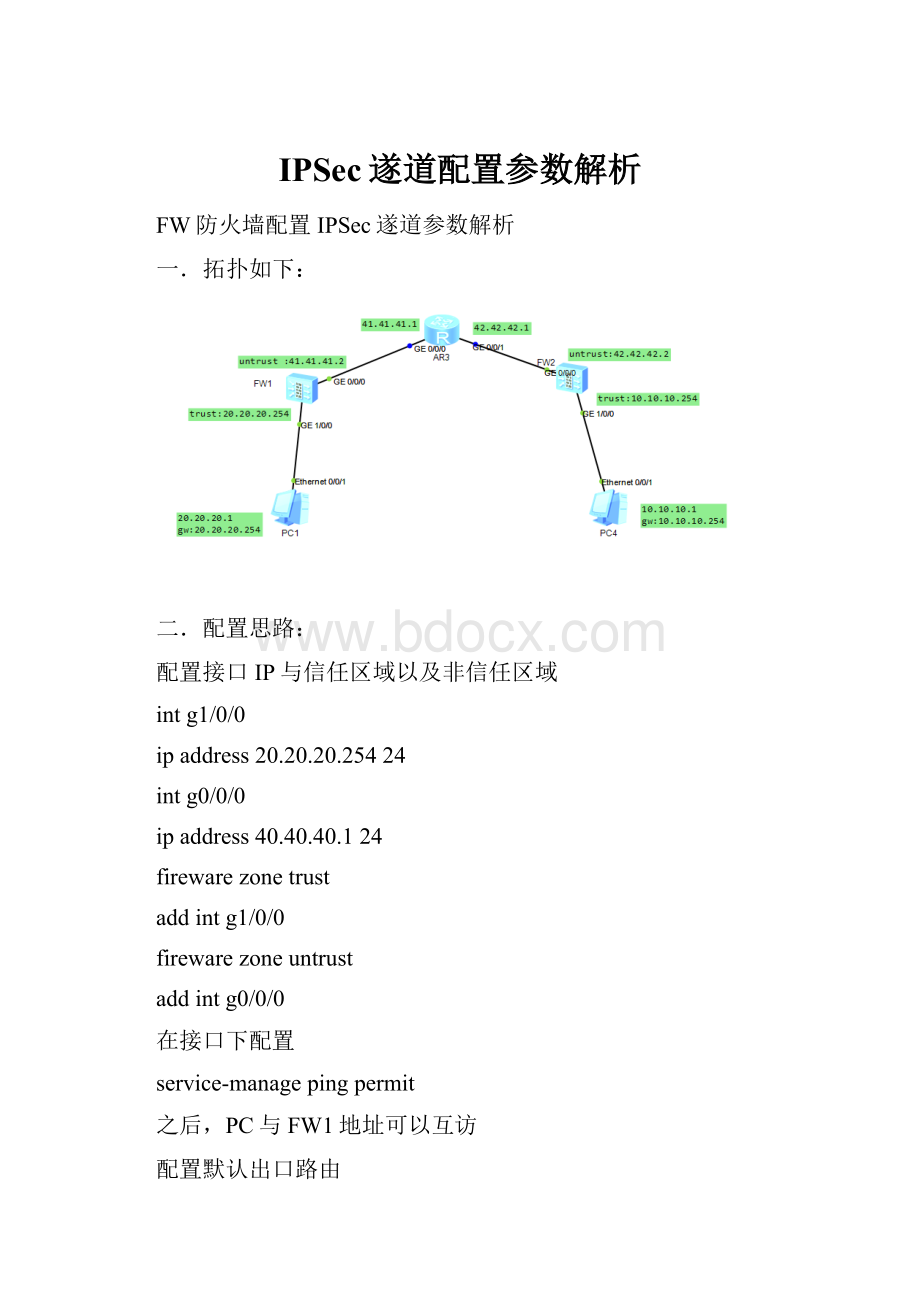
一.拓扑如下:
二.配置思路:
配置接口IP与信任区域以及非信任区域
intg1/0/0
ipaddress20.20.20.25424
intg0/0/0
ipaddress40.40.40.124
firewarezonetrust
addintg1/0/0
firewarezoneuntrust
addintg0/0/0
在接口下配置
service-managepingpermit
之后,PC与FW1地址可以互访
配置默认出口路由
iproute-static0.0.0.0041.41.41.1
配置IPsec遂道
*******************************************************************************
配置IKEProposal
ikeproposal10
authentiaction-methodpre-share
authentication-algorithmsha1
encryption-algorithm3des
dhgroup2
配置IPsecproposal
ipsecproposalmyset(myset_fw1/myset_fw2在不同防火墙上配置不同)
transformesp
espauthentication-algorithmsha1
espencryption-algorithm3des
配置IKEpeer
ikepeerfw(fw2/fw1,同上,在不同防火墙上配置不同)
pre-shared-keyhuawei123(密码,两端必须设置一致)
ike-proposal10
remote-address(配置为对端FW的非信任区IP,42.42.42.2/41.41.41.2,为遂道两侧地址,这边设置为对端地址)
遂道内流量匹配才可以通过,另外一个防火墙流量应该反过来
*******************************************************************************
配置遂道内流量放通策略,并且在对应接口上应用
aclnumber3000
rulepermitipsource20.20.20.00.0.0.255destination10.10.10.00.0.0.255
配置FW上IPsecPolicy
ipsecpolicymymap10isakmp
securityacl3000
ike-peerfw2
tunnellocal(配置为本端FW的非信任区IP,41.41.41.2/42.42.42.2,为遂道两侧地址,这边设置为本端地址)
proposalmyset(myset_fw1/myset_fw2,同上,在不同防火墙上配置不同)
配置应用IPsecpolicy到接口(untrust流量出去的接口)
interfaceg0/0/0
ipsecpolicymymap
*******************************************************************************
配置流量放通策略
下面是FW2上配置数据,分别是
到目标10.10.10.0的流量放通,从10.10.10.0出去流量放通
到目标42.42.42.0的流量放通,从42.42.42.0出去流量放通
FW1上配置数据,应该是
到目标20.20.20.0的流量放通,从20.20.20.0出去流量放通
到目标41.41.41.0的流量放通,从41.41.41.0出去流量放通
[FW2-policy-security]
#
security-policy
rulename20in
destination-zonetrust
destination-address10.10.10.00.0.0.255
actionpermit
rulenametest11
source-address42.42.42.0mask255.255.255.0
actionpermit
rulenametest12
destination-address42.42.42.0mask255.255.255.0
actionpermit
rulename20out
source-zonetrust
source-address10.10.10.0mask255.255.255.0
actionpermit
#return
[FW2-policy-security]
三.结果验证:
从PC1pingPC4,可达
。
从PC4pingPC1,可达。
抓包分析,可以看到上面PC1与PC4互相ping可达,在FW1--FW2之间抓包,PC1与PC4的IP地址已经隐藏,完全通过加密遂道传输,只能看到遂道两侧地址进行数据交互。
四.完整数据:
2020-03-3013:
03:
04.390
!
SoftwareVersionV500R005C10SPC300
#
sysnameFW1
#
l2tpdomainsuffix-separator@
#
ipsecsha2compatibleenable
#
undotelnetserverenable
undotelnetipv6serverenable
#
clocktimezoneUTCadd00:
00:
00
#
updateschedulelocation-sdbweeklySun22:
05
#
firewalldefendactiondiscard
#
bannerenable
#
user-manageweb-authenticationsecurityport8887
undoprivacy-statementenglish
undoprivacy-statementchinese
page-setting
user-managesecurityversiontlsv1.1tlsv1.2
password-policy
levelhigh
user-managesingle-sign-onad
user-managesingle-sign-ontsm
user-managesingle-sign-onradius
user-manageauto-synconline-user
#
web-managersecurityversiontlsv1.1tlsv1.2
web-managerenable
web-managersecurityenable
#
firewalldataplanetomanageplaneapplication-apperceivedefault-actiondrop
#
undoipslogmergeenable
#
decodinguri-cachedisable
#
updatescheduleips-sdbdaily05:
37
updatescheduleav-sdbdaily05:
37
updateschedulesa-sdbdaily05:
37
updateschedulecncdaily05:
37
updateschedulefile-reputationdaily05:
37
#
ipvpn-instancedefault
ipv4-family
#
time-rangeworktime
period-range08:
00:
00to18:
00:
00working-day
#
aclnumber3000
rule5permitipsource20.20.20.00.0.0.255destination10.10.10.00.0.0.255
#
ipsecproposalmyset_fw1
espauthentication-algorithmsha1
espencryption-algorithm3des
#
ikeproposaldefault
encryption-algorithmaes-256aes-192aes-128
dhgroup14
authentication-algorithmsha2-512sha2-384sha2-256
authentication-methodpre-share
integrity-algorithmhmac-sha2-256
prfhmac-sha2-256
ikeproposal10
encryption-algorithm3des
dhgroup2
authentication-algorithmsha1
authentication-methodpre-share
integrity-algorithmhmac-sha2-256
prfhmac-sha2-256
#
ikepeerfw2
pre-shared-key%^%#]#ZG'w_qoVDFBV)u$D>YU)u'=*CX~XO-gSV\eGz!
%^%#
ike-proposal10
remote-address42.42.42.2
#
ipsecpolicymymap10isakmp
securityacl3000
ike-peerfw2
proposalmyset_fw1
tunnellocal41.41.41.2
#
aaa
authentication-schemedefault
authentication-schemeadmin_local
authentication-schemeadmin_radius_local
authentication-schemeadmin_hwtacacs_local
authentication-schemeadmin_ad_local
authentication-schemeadmin_ldap_local
authentication-schemeadmin_radius
authentication-schemeadmin_hwtacacs
authentication-schemeadmin_ad
authorization-schemedefault
accounting-schemedefault
domaindefault
service-typeinternetaccessssl-vpnl2tpike
internet-accessmodepassword
referenceusercurrent-domain
manager-useraudit-admin
passwordcipher@%@%jzvO,YbEn-I6AQ8(vHYBT7cC-/yn service-typewebterminal level15 manager-userapi-admin passwordcipher@%@%UcRX level15 manager-useradmin passwordcipher@%@%Ed#lS9$SO~k5hyTi5js(viI}Z{3FXV,ZePW}%$V9[qSAiI#v@%@% service-typewebterminal level15 rolesystem-admin roledevice-admin roledevice-admin(monitor) roleaudit-admin bindmanager-useraudit-adminroleaudit-admin bindmanager-useradminrolesystem-admin # l2tp-groupdefault-lns # interfaceGigabitEthernet0/0/0 undoshutdown ipaddress41.41.41.2255.255.255.0 service-managepingpermit ipsecpolicymymap # interfaceGigabitEthernet1/0/0 undoshutdown ipaddress20.20.20.254255.255.255.0 service-managepingpermit # interfaceGigabitEthernet1/0/1 undoshutdown # interfaceGigabitEthernet1/0/2 undoshutdown # interfaceGigabitEthernet1/0/3 undoshutdown # interfaceGigabitEthernet1/0/4 undoshutdown # interfaceGigabitEthernet1/0/5 undoshutdown # interfaceGigabitEthernet1/0/6 undoshutdown # interfaceVirtual-if0 # interfaceNULL0 # firewallzonelocal setpriority100 # firewallzonetrust setpriority85 addinterfaceGigabitEthernet1/0/0 # firewallzoneuntrust setpriority5 addinterfaceGigabitEthernet0/0/0 # firewallzonedmz setpriority50 # iproute-static0.0.0.00.0.0.041.41.41.1 # undosshservercompatible-ssh1xenable sshauthentication-typedefaultpassword sshservercipheraes256_ctraes128_ctr sshserverhmacsha2_256sha1 sshclientcipheraes256_ctraes128_ctr sshclienthmacsha2_256sha1 # firewalldetectftp # user-interfacecon0 authentication-modeaaa user-interfacevty04 authentication-modeaaa protocolinboundssh user-interfacevty1620 # pkirealmdefault # sa # location # multi-linkif modeproportion-of-weight # right-managerserver-group # device-classification device-grouppc device-groupmobile-terminal device-groupundefined-group # user-manageserver-synctsm # security-policy rulename10out source-zonetrust source-address20.20.20.00.0.0.255 actionpermit rulename10in destination-zonetrust destination-address20.20.20.00.0.0.255 actionpermit rulenametest1 destination-address41.41.41.0mask255.255.255.0 actionpermit rulenametest2 source-address41.41.41.0mask255.255.255.0 actionpermit # auth-policy # traffic-policy # policy-based-route # nat-policy # quota-policy # pcp-policy # dns-transparent-policy # rightm-policy # return 2020-03-3013: 08: 35.340 ! SoftwareVersionV500R005C10SPC300 # sysnameFW2 # l2tpdomainsuffix-separator@ # ipsecsha2compatibleenable # undotelnetserverenable undotelnetipv6serverenable # clocktimezoneUTCadd00: 00: 00 # updateschedulelocation-sdbweeklySun05: 09 # firewalldefendactiondiscard # bannerenable # user-manageweb-authenticationsecurityport8887 undoprivacy-statementenglish undoprivacy-statementchinese page-setting user-managesecurityversiontlsv1.1tlsv1.2 password-policy levelhigh user-managesingle-sign-onad user-managesingle-sign-ontsm user-managesingle-sign-onradius user-manageauto-synconline-user # web-managersecurityversiontlsv1.1tlsv1.2 web-managerenable web-managersecurityenable # firewalldataplanetomanageplaneapplication-apperceivedefault-actiondrop # undoipslogmergeenable # decodinguri-cachedisable # updatescheduleips-sdbdaily06: 18 updatescheduleav-sdbdaily06: 18 updateschedulesa-sdbdaily06: 18 updateschedulecncdaily06: 18 updateschedulefile-reputationdaily06: 18 # ipvpn-instancedefault ipv4-family # time-rangeworktime period-range08: 00: 00to18: 00: 00working-day # aclnumber3000 rule5permitipsource10.10.10.00.0.0.255destination20.20.20.00.0.0.255 # ipsecproposalmyset_fw2 espauthentication-algorithmsha1 espencryption-algorithm3des # ikeproposaldefault encryption-algorithmaes-256aes-192aes-128 dhgroup14 authentication-algorithmsha2-512sha2-384sha2-256 authentication-methodpre-share integrity-algorithmhmac-sha2-256 prfhmac-sha2-256 ikeproposal10 encryption-algorithm3des dhgroup2 authentication-algorithmsha1 authentication-methodpre-share integrity-algorithmhmac-sha2-256 prfhmac-sha2-256 # ikepeerfw1 pre-shared-key%^%#IUDj"*: Xs=;eNi~P21R4fO2$B4t: ~Uhe^2#Q#: +(%^%# ike-proposal10 remote-address41.41.41.2 # ipsecpolicymymap10isakmp securityacl3000 ike-peerfw1 proposalmyset_fw2 tunnellocal42.42.42.2 # aaa authentication-schemedefault authentication-schemeadmin_local authentication-schemeadmin_radius_local authentication-schemeadmin_hwtacacs_local authentication-schemeadmin_ad_local
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- IPSec 配置 参数 解析
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 《城市规划基本知识》深刻复习要点.docx
《城市规划基本知识》深刻复习要点.docx
 赵体1、简介、运笔(楷书教学课件).ppt
赵体1、简介、运笔(楷书教学课件).ppt
 室内装修预算书完整版(模版).xls
室内装修预算书完整版(模版).xls
