 22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs.docx
22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs.docx
- 文档编号:3878193
- 上传时间:2022-11-26
- 格式:DOCX
- 页数:16
- 大小:24.48KB
22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs.docx
《22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs.docx》由会员分享,可在线阅读,更多相关《22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs.docx(16页珍藏版)》请在冰豆网上搜索。
22090140060000meetingminutesofthesecurityandmanagementplaneproceduresadhocs
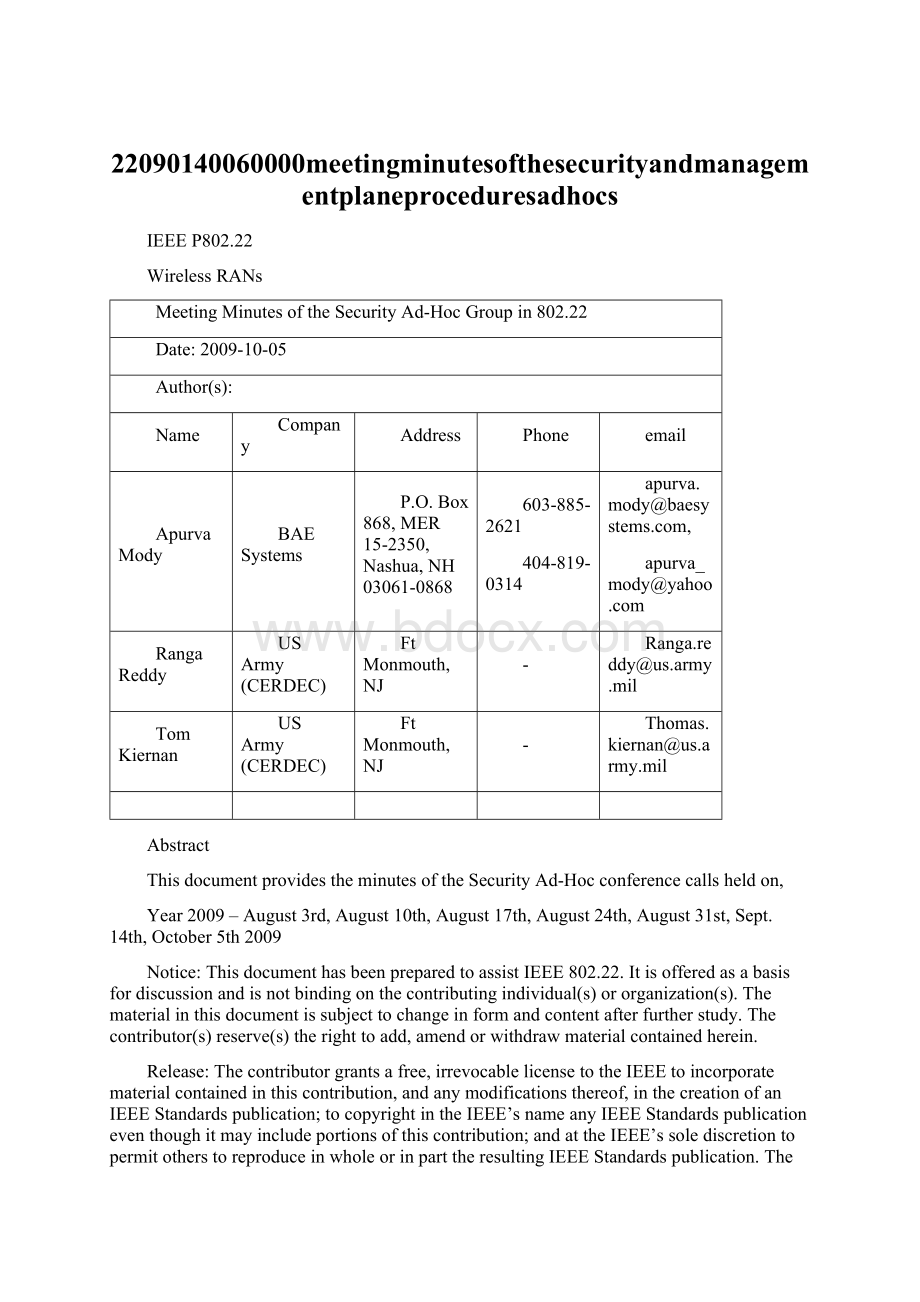
IEEEP802.22
WirelessRANs
MeetingMinutesoftheSecurityAd-HocGroupin802.22
Date:
2009-10-05
Author(s):
Name
Company
Address
Phone
ApurvaMody
BAESystems
P.O.Box868,MER15-2350,Nashua,NH03061-0868
603-885-2621
404-819-0314
apurva.mody@,
apurva_mody@
RangaReddy
USArmy(CERDEC)
FtMonmouth,NJ
-
Ranga.reddy@us.army.mil
TomKiernan
USArmy(CERDEC)
FtMonmouth,NJ
-
Thomas.kiernan@us.army.mil
Abstract
ThisdocumentprovidestheminutesoftheSecurityAd-Hocconferencecallsheldon,
Year2009–August3rd,August10th,August17th,August24th,August31st,Sept.14th,October5th2009
Notice:
ThisdocumenthasbeenpreparedtoassistIEEE802.22.Itisofferedasabasisfordiscussionandisnotbindingonthecontributingindividual(s)ororganization(s).Thematerialinthisdocumentissubjecttochangeinformandcontentafterfurtherstudy.Thecontributor(s)reserve(s)therighttoadd,amendorwithdrawmaterialcontainedherein.
Release:
Thecontributorgrantsafree,irrevocablelicensetotheIEEEtoincorporatematerialcontainedinthiscontribution,andanymodificationsthereof,inthecreationofanIEEEStandardspublication;tocopyrightintheIEEE’snameanyIEEEStandardspublicationeventhoughitmayincludeportionsofthiscontribution;andattheIEEE’ssolediscretiontopermitotherstoreproduceinwholeorinparttheresultingIEEEStandardspublication.ThecontributoralsoacknowledgesandacceptsthatthiscontributionmaybemadepublicbyIEEE802.22.
PatentPolicyandProcedures:
ThecontributorisfamiliarwiththeIEEE802PatentPolicyandProcedures
//standards.ieee.org/guides/bylaws/sb-bylaws.pdf>,includingthestatement"IEEEstandardsmayincludetheknownuseofpatent(s),includingpatentapplications,providedtheIEEEreceivesassurancefromthepatentholderorapplicantwithrespecttopatentsessentialforcompliancewithbothmandatoryandoptionalportionsofthestandard."EarlydisclosuretotheWorkingGroupofpatentinformationthatmightberelevanttothestandardisessentialtoreducethepossibilityfordelaysinthedevelopmentprocessandincreasethelikelihoodthatthedraftpublicationwillbeapprovedforpublication.PleasenotifytheChair 1.August3rd2009–SecurityAd-HocConferenceCallMeetingMinutes MeetingMinutes 1.Attendance ApurvaMody–BAESystems GeraldChouinard-CRC RangaReddy–USArmy WinstonCaldwell–Fox 2.1Agenda ∙Attendance ∙Chairaskedifeveryoneattending was familiarwiththeIEEEpatentpolicy-http: //standards.ieee.org/board/pat/pat-slideset.pdf-Everyonewasfamiliar. ∙Minutes of alltheSecurityAd-HocConferenceCalls previouslyheld canbefoundat–https: //mentor.ieee.org/802.22/dcn/08/22-08-0163-22-0000-meeting-minutes-of-the-security-ad-hoc-group-in-802-22.doc ∙DiscussiononProtectionMechanismsforCo-existenceBeaconingPackets–ledbyRangaReddy.https: //mentor.ieee.org/802.22/dcn/08/22-08-0296-03-0000-cbp-security-protection-mechanisms.doc ∙RecommendedTextforSection7onSecurityin802.22 –includedinDraftv2.0canbefoundathttps: //mentor.ieee.org/802.22/dcn/08/22-08-0174-18-0000-recommended-text-for-section-7-on-security-in-802-22.doc ∙ReferenceDocument-TableofContentsforSection7.Thereferencedocumentfortheproposedtextcanbefoundat https: //mentor.ieee.org/802.22/file/08/22-08-0165-00-0000-table-of-content-for-the-security-section-in-802-22.doc ∙ReferenceDocument-ScopeandtheWorkplanfortheSecurityAd-HocGroup–https: //mentor.ieee.org/802.22/file/08/22-08-0159-00-0000-scope-agenda-workplan-and-timeline-for-the-security-ad-hoc-in-802-22.doc ∙ReferenceDocument-PresentationonthePRMandSecurityEnhancementsin802.22–802.22ThreatAnalysis https: //mentor.ieee.org/802.22/dcn/08/22-08-0083-08-0000-security-and-prm-enhancements-in-80222-v3.ppt ∙ProposedReferenceArchitecturefor802.22-https: //mentor.ieee.org/802.22/dcn/08/22-08-0121-10-0000-text-on-protocol-reference-model-enhancements-in-802-22.doc ∙802.22DatabaseInterfaceArchitectureandSecurityMechanisms-https: //mentor.ieee.org/802.22/dcn/09/22-09-0111-02-0000-database-interface-architecture-and-security-mechanisms.ppt ∙WhitespaceDatabaseService-https: //mentor.ieee.org/802.19/dcn/09/19-09-0047-00-tvws-white-spaces-database.ppt MinutesandDiscussions ∙Comments667,668,673,674,675,676,679and680wereresolved.TheproposedresolutionscanbefoundintheDocumenthttps: //mentor.ieee.org/802.22/dcn/09/22-09-0120-03-0000-wran-draft-2-0-ballot-comment-database.xls ∙Comment#662–GeraldChouinard.Thereweresomediscussionsonthiscomment.Gerald’scommentistokeepthecomplexityofthesecuritysuitesin802.22lowsothatthereisnotahighbarriertothemarket ∙RangaReddysuggestedthatwhenthesecurityad-hocstartedexploringthearchitectureforthesecurityin802.22,wefoundthe802.16modelmostappropriate.Manythingsfromthe802.16securityarchitecturehavebeenstreamlined.Thereisalsoanoption,thatifauserdoesnothaveacapabilitytoperformsecurityrelatedfunctionssuchasencryption/authentication,itmaytelltheBSandtheBSmayeitherchoosetoservetheuserwithnosecurityfeaturesoritmaydecidetode-authorizetheuserfromthenetwork. ∙ApurvaModysuggestedthatthesecurityad-hocwillconsiderprovidingsome802.11typeofmechanismssothatitmayfacilitatequickeradoptionofthestandard. ∙RangaReddysuggestedthatsecurityad-hocisalreadyconsideringaddingExtensivleAuthenticationProtocol(EAP)whichwillallowtheserviceproviderstoautomaticallygeneratethecertificatesandkeys. ∙RangaReddysuggestedthatwewaituntilallthecommentsareresolvedandthenre-vistithiscommenttoseeifsomethingcanbedonetoreducethecomplexity. ∙Winston–Weneedtokeepinmindthemarketwhere802.22islikelytobedeployedmore–notAfricabuttheUS ∙ApurvaModysuggestedthatlookingatthetrendsin802.16/WiMAX,itlookedlike802.22maybeadoptedmorequicklyinothercountrieswithlesserbroadbandpenetrationascomparedtotheUS. 2.August10th2009–SecurityAd-HocConferenceCallMeetingMinutes MeetingMinutes 1.Attendance ApurvaMody–BAESystems GeraldChouinard-CRC RangaReddy–USArmy WinstonCaldwell–Fox 2.1Agenda ∙Attendance ∙Chairaskedifeveryoneattending was familiarwiththeIEEEpatentpolicy-http: //standards.ieee.org/board/pat/pat-slideset.pdf-Everyonewasfamiliar. ∙Minutes of alltheSecurityAd-HocConferenceCalls previouslyheld canbefoundat–https: //mentor.ieee.org/802.22/dcn/08/22-08-0163-22-0000-meeting-minutes-of-the-security-ad-hoc-group-in-802-22.doc ∙DiscussiononProtectionMechanismsforCo-existenceBeaconingPackets–ledbyRangaReddy.https: //mentor.ieee.org/802.22/dcn/08/22-08-0296-03-0000-cbp-security-protection-mechanisms.doc ∙RecommendedTextforSection7onSecurityin802.22 –includedinDraftv2.0canbefoundathttps: //mentor.ieee.org/802.22/dcn/08/22-08-0174-18-0000-recommended-text-for-section-7-on-security-in-802-22.doc ∙ReferenceDocument-TableofContentsforSection7.Thereferencedocumentfortheproposedtextcanbefoundat https: //mentor.ieee.org/802.22/file/08/22-08-0165-00-0000-table-of-content-for-the-security-section-in-802-22.doc ∙ReferenceDocument-ScopeandtheWorkplanfortheSecurityAd-HocGroup–https: //mentor.ieee.org/802.22/file/08/22-08-0159-00-0000-scope-agenda-workplan-and-timeline-for-the-security-ad-hoc-in-802-22.doc ∙ReferenceDocument-PresentationonthePRMandSecurityEnhancementsin802.22–802.22ThreatAnalysis https: //mentor.ieee.org/802.22/dcn/08/22-08-0083-08-0000-security-and-prm-enhancements-in-80222-v3.ppt ∙ProposedReferenceArchitecturefor802.22-https: //mentor.ieee.org/802.22/dcn/08/22-08-0121-10-0000-text-on-protocol-reference-model-enhancements-in-802-22.doc ∙802.22DatabaseInterfaceArchitectureandSecurityMechanisms-https: //mentor.ieee.org/802.22/dcn/09/22-09-0111-02-0000-database-interface-architecture-and-security-mechanisms.ppt ∙WhitespaceDatabaseService-https: //mentor.ieee.org/802.19/dcn/09/19-09-0047-00-tvws-white-spaces-database.ppt MinutesandDiscussions ∙DiscussionsonsecurityaspectswiththeexternalWhitespacedatabasewascarriedout. ∙RangaReddybroughttotheattentionofthegroupthattheWhitespacesDatabasesGrouphasstartedtalkingaboutthesecurityissuesofthedatabasewiththeWhitespaceDevice.ThisdocumentincludesPublicKeyInfrastructure(PKI),TransportSecurityandDeviceSecurity. ∙PKI-ForPKI,X.509baseduseofcertificatesissuggestedforkeyexchange.TheseX.509certificateswillholdanentitynameintheSubjectAltNamefield,followingtheconventionoftheWorldWideWeb.A2048-bitRSAkeyforinitialdeploymentissuggestedwithforwardcompatibilityforkeysizeincreases.Usekeyrolloverproceduresbasedonpre-publishedsupersessiontoensurelong-termstabilityofthesecurityarchitectureisproposed.TheOSCPprotocol(RFC2560)maybeusedbyWSDstoverifythatWSSPcertificateshavenotbeenrevokedbytheRepository. ∙TransportSecurity–TransportLayerSecurityorTLS(RFC4346,thoughitissometimesbetterknownbyitsoldname,SecureSocketsLayerorSSL)issuggested.TLSprovidesauthentication,integrity
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- 22090140060000 meetingminutesofthesecurityandmanagementplaneproceduresadhocs
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
链接地址:https://www.bdocx.com/doc/3878193.html


 广东省普通高中学业水平考试数学科考试大纲Word文档下载推荐.docx
广东省普通高中学业水平考试数学科考试大纲Word文档下载推荐.docx
