 SitetoSite VPN 配置实例共享密钥.docx
SitetoSite VPN 配置实例共享密钥.docx
- 文档编号:29531643
- 上传时间:2023-07-24
- 格式:DOCX
- 页数:16
- 大小:30.46KB
SitetoSite VPN 配置实例共享密钥.docx
《SitetoSite VPN 配置实例共享密钥.docx》由会员分享,可在线阅读,更多相关《SitetoSite VPN 配置实例共享密钥.docx(16页珍藏版)》请在冰豆网上搜索。
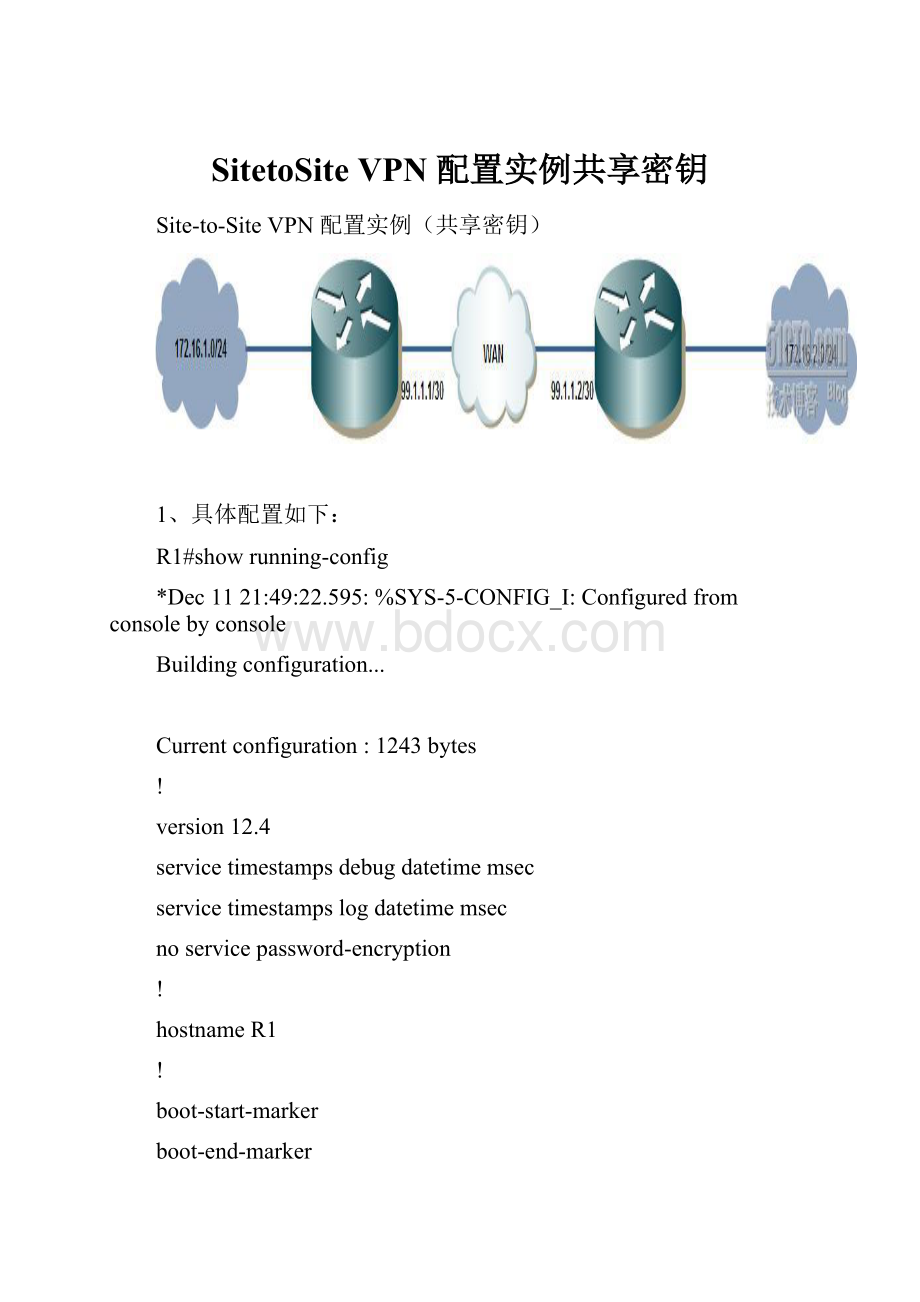
SitetoSiteVPN配置实例共享密钥
Site-to-SiteVPN配置实例(共享密钥)
1、具体配置如下:
R1#showrunning-config
*Dec1121:
49:
22.595:
%SYS-5-CONFIG_I:
Configuredfromconsolebyconsole
Buildingconfiguration...
Currentconfiguration:
1243bytes
!
version12.4
servicetimestampsdebugdatetimemsec
servicetimestampslogdatetimemsec
noservicepassword-encryption
!
hostnameR1
!
boot-start-marker
boot-end-marker
!
!
noaaanew-model
!
resourcepolicy
!
ipsubnet-zero
!
!
ipcef
!
!
!
cryptoisakmppolicy110
encr3des
hashmd5
authenticationpre-share
group2
cryptoisakmpkeyciscoaddress99.1.1.2
!
!
cryptoipsectransform-setvpnah-md5-hmacesp-desesp-sha-hmac
!
cryptomapsitevpn10ipsec-isakmp
setpeer99.1.1.2
settransform-setvpn
matchaddress110
!
!
!
!
interfaceLoopback0
ipaddress172.16.1.1255.255.255.0
!
interfaceFastEthernet0/0
ipaddress99.1.1.1255.255.255.252
duplexhalf
!
interfaceEthernet1/0
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/1
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/2
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/3
noipaddress
shutdown
duplexhalf
!
ipclassless
iproute0.0.0.00.0.0.099.1.1.2
!
noiphttpserver
noiphttpsecure-server
!
!
access-list110permitip172.16.1.00.0.0.255172.16.2.00.0.0.255
!
!
!
!
control-plane
!
!
!
!
!
!
gatekeeper
shutdown
!
!
linecon0
stopbits1
lineaux0
linevty04
!
!
end
R2#showrunning-config
Buildingconfiguration...
Currentconfiguration:
1263bytes
!
version12.4
servicetimestampsdebugdatetimemsec
servicetimestampslogdatetimemsec
noservicepassword-encryption
!
hostnameR2
!
boot-start-marker
boot-end-marker
!
!
noaaanew-model
!
resourcepolicy
!
ipsubnet-zero
!
!
ipcef
!
!
!
!
cryptoisakmppolicy110
encr3des
hashmd5
authenticationpre-share
group2
cryptoisakmpkeyciscoaddress99.1.1.1
!
!
cryptoipsectransform-setvpnah-md5-hmacesp-desesp-sha-hmac
!
cryptomapsitevpn10ipsec-isakmp
setpeer99.1.1.1
settransform-setvpn
matchaddress110
!
!
!
!
interfaceLoopback0
ipaddress172.16.2.1255.255.255.0
!
interfaceFastEthernet0/0
ipaddress99.1.1.2255.255.255.252
duplexhalf
cryptomapsitevpn
!
interfaceEthernet1/0
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/1
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/2
noipaddress
shutdown
duplexhalf
!
interfaceEthernet1/3
noipaddress
shutdown
duplexhalf
!
ipclassless
iproute0.0.0.00.0.0.099.1.1.1
!
noiphttpserver
noiphttpsecure-server
!
!
access-list110permitip172.16.2.00.0.0.255172.16.1.00.0.0.255
!
!
!
!
control-plane
!
!
!
!
!
!
gatekeeper
shutdown
!
!
linecon0
stopbits1
lineaux0
linevty04
!
!
end
2、验证配置
R2#debugcryptoipsec
CryptoIPSECdebuggingison
R2#ping172.16.1.1source172.16.2.1
Typeescapesequencetoabort.
Sending5,100-byteICMPEchosto172.16.1.1,timeoutis2seconds:
Packetsentwithasourceaddressof172.16.2.1
*Dec1121:
52:
54.995:
IPSEC(sa_request):
(keyeng.msg.)OUTBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=AH,transform=ah-md5-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0xC34D28FA(3276613882),conn_id=0,keysize=0,flags=0x400A
*Dec1121:
52:
54.999:
IPSEC(sa_request):
(keyeng.msg.)OUTBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=ESP,transform=esp-desesp-sha-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0x397AFB16(964360982),conn_id=0,keysize=0,flags=0x400A
*Dec1121:
52:
56.339:
IPSEC(validate_proposal_request):
proposalpart#1,
(keyeng.msg.)INBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=AH,transform=ah-md5-hmac (Tunnel),
lifedur=0sand0kb,
spi=0x0(0),conn_id=0,keysize=0,flags=0x2
*Dec1121:
52:
56.347:
IPSEC(validate_proposal_request):
proposalpart#2,
(keyeng.msg.)INBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=ESP,transform=esp-desesp-sha-hmac (Tunnel),
lifedur=0sand0kb,
spi=0x0(0),conn_id=0,keysize=0,flags=0x2
*Dec1121:
52:
56.351:
Cryptomapdb:
proxy_match
srcaddr :
172.16.2.0
dstaddr :
172.16.1.0
protocol :
0
srcport :
0
dstport :
0
*Dec1121:
52:
56.367:
IPSEC(key_engine):
gotaqueueeventwith4keimessages
*Dec1121:
52:
56.367:
IPSEC(initialize_sas):
(keyeng.msg.)INBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=AH,transform=ah-md5-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0xC34D28FA(3276613882),conn_id=0,keysize=0,flags=0x2
*Dec1121:
52:
56.371:
IPSEC(initialize_sas):
(keyeng.msg.)OUTBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=AH,transform=.!
!
!
!
Successrateis80percent(4/5),round-tripmin/avg/max=32/68/112ms
R2#ah-md5-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0x303B33D8(809186264),conn_id=0,keysize=0,flags=0xA
*Dec1121:
52:
56.375:
IPSEC(initialize_sas):
(keyeng.msg.)INBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=ESP,transform=esp-desesp-sha-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0x397AFB16(964360982),conn_id=0,keysize=0,flags=0x2
*Dec1121:
52:
56.379:
IPSEC(initialize_sas):
(keyeng.msg.)OUTBOUNDlocal=99.1.1.2,remote=99.1.1.1,
local_proxy=172.16.2.0/255.255.255.0/0/0(type=4),
remote_proxy=172.16.1.0/255.255.255.0/0/0(type=4),
protocol=ESP,transform=esp-desesp-sha-hmac (Tunnel),
lifedur=3600sand4608000kb,
spi=0x6D84A16(114838038),conn_id=0,keysize=0,flags=0xA
*Dec1121:
52:
56.383:
Cryptomapdb:
proxy_match
srcaddr :
172.16.2.0
dstaddr :
172.16.1.0
protocol :
0
srcport :
0
dstport :
0
*Dec1121:
52:
56.387:
IPSEC(crypto_ipsec_sa_find_ident_head):
reconnectingwiththesameproxiesand99.1.1.1
*Dec1121:
52:
56.391:
IPSec:
Flow_switchingAllocatedflowforsibling80000002
*Dec1121:
52:
56.391:
IPSEC(policy_db_add_ident):
src172.16.2.0,dest172.16.1.0,dest_port0
*Dec1121:
52:
56.395:
IPSEC(create_sa):
sacreated,
(sa)sa_dest=99.1.1.2,sa_proto=51,
sa_spi=0xC34D28FA(3276613882),
sa_trans=ah-md5-hmac,sa_conn_id=2001
*Dec1121:
52:
56.395:
IPSEC(create_sa):
sacreated,
(sa)sa_dest=99.1.1.1,sa_proto=51,
sa_spi=0x303B33D8(809186264),
sa_trans=ah-md5-hmac,sa_conn_id=2002
*Dec1121:
52:
56.399:
IPSEC(create_sa):
sacreated,
(sa)sa_dest=99.1.1.2,sa_proto=50,
sa_spi=0x397AFB16(964360982),
sa_trans=esp-desesp-sha-hmac,sa_conn_id=2001
*Dec1121:
52:
56.403:
IPSEC(create_sa):
sacreated,
(sa)sa_dest=99.1.1.1,sa_proto=50,
sa_spi=0x6D84A16(114838038),
sa_trans=esp-desesp-sha-hmac,sa_conn_id=2002
R2#ping172.16.1.1source172.16.2.1
Typeescapesequencetoabort.
Sending5,100-byteICMPEchosto172.16.1.1,timeoutis2seconds:
Packetsentwithasourceaddressof172.16.2.1
!
!
!
!
!
Successrateis100percent(5/5),round-tripmin/avg/max=8/36/108ms
R2#shcryptoipsecsa
interface:
FastEthernet0/0
Cryptomaptag:
sitevpn,localaddr99.1.1.2
protectedvrf:
(none)
local ident(addr/mask/prot/port):
(172.16.2.0/255.255.255.0/0/0)
remoteident(addr/mask/prot/port):
(172.16.1.0/255.255.255.0/0/0)
current_peer99.1.1.1port500
PERMIT,flags={origin_is_acl,}
#pktsencaps:
9,#pktsencrypt:
9,#pktsdigest:
9
#pktsdecaps:
9,#pktsdecrypt:
9,#pktsverify:
9
#pktscompressed:
0,#pktsdecompressed:
0
#pktsnotcompressed:
0,#pktscompr.failed:
0
#pktsnotdecompressed:
0,#pktsdecompressfailed:
0
#senderrors1,#recverrors0
localcryptoendpt.:
99.1.1.2,remotecryptoendpt.:
99.1.1.1
pathmtu1500,ipmtu1500
currentoutboundspi:
0x6D84A16(114838038)
inboundespsas:
spi:
0x397AFB16(964360982)
transform:
esp-desesp-sha-hmac,
inusesettings={Tunnel,}
connid:
2001,flow_id:
SW:
1,cryptomap:
sitevpn
satiming:
remainingkeylifetime(k/sec):
(4497696/3536)
IVsize:
8bytes
replaydetectionsupport:
Y
Status:
ACTIVE
inboundahsas:
spi:
0xC34D28FA(3276613882)
transform:
ah-md5-hmac,
inusesettings={Tunnel,}
connid:
2001,flow_id:
SW:
1,cryptomap:
sitevpn
satiming:
remainingkeylifetime(k/sec):
(4497696/3535)
replaydetectionsupport:
Y
Status:
ACTIVE
inboundpcpsas:
outboundespsas:
spi:
0x6D84A16(114838038)
transform:
esp-desesp-sha-hmac,
inusesettings={Tunnel,}
connid:
2002,flow_id:
SW:
2,cryptomap:
sitevpn
satiming:
remainingkeylifetime(k/sec):
(4497696/3535)
IVsize:
8byt
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- SitetoSite VPN 配置实例共享密钥 配置 实例 共享 密钥
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 《贝的故事》教案4.docx
《贝的故事》教案4.docx
