 LAN TO LAN VPNWord文件下载.docx
LAN TO LAN VPNWord文件下载.docx
- 文档编号:21627006
- 上传时间:2023-01-31
- 格式:DOCX
- 页数:23
- 大小:428.35KB
LAN TO LAN VPNWord文件下载.docx
《LAN TO LAN VPNWord文件下载.docx》由会员分享,可在线阅读,更多相关《LAN TO LAN VPNWord文件下载.docx(23页珍藏版)》请在冰豆网上搜索。
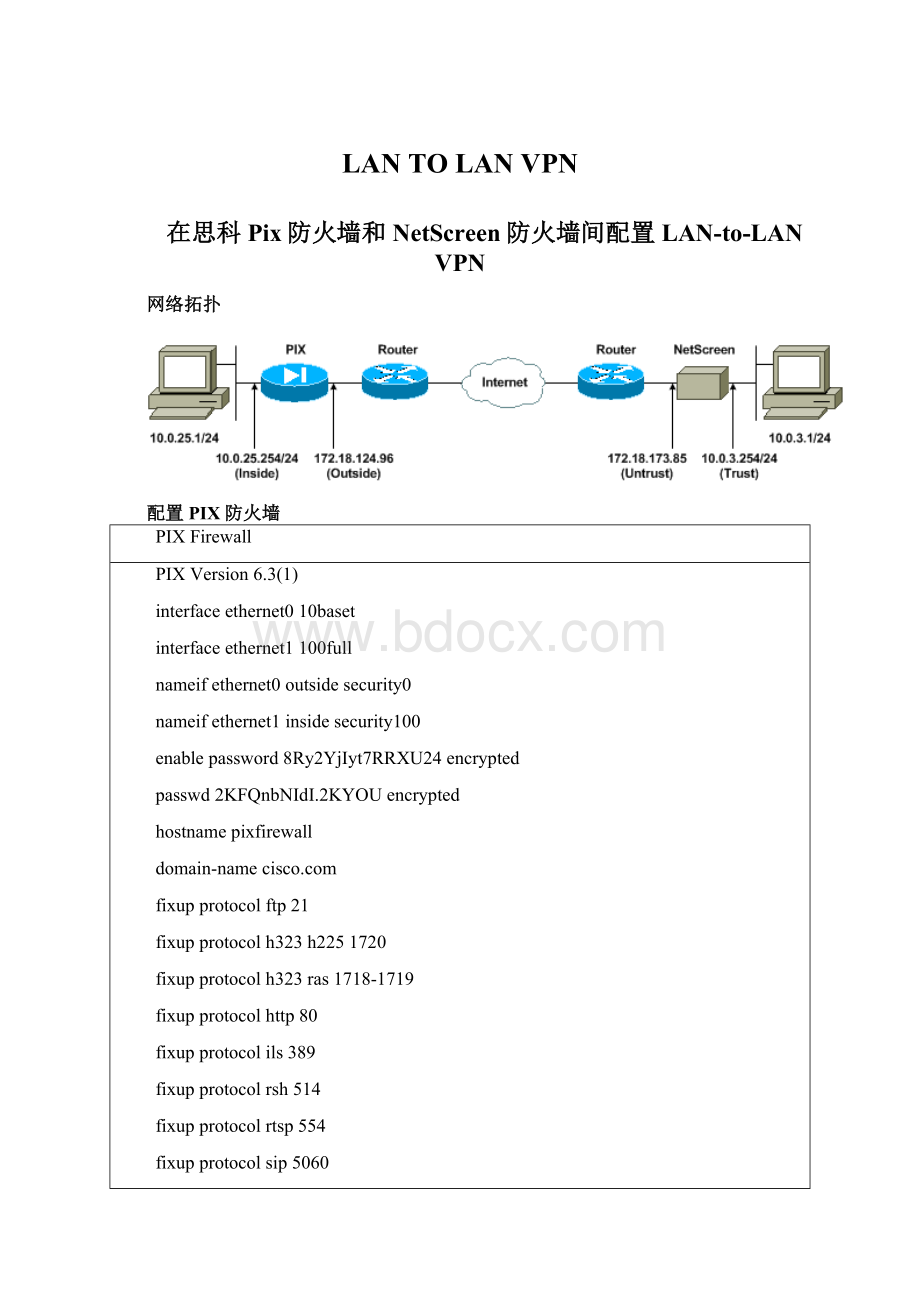
---tobypasstheNetworkAddressTranslation(NAT)process
access-listnonatpermitip10.0.25.0255.255.255.010.0.3.0255.255.255.0
pagerlines24
loggingon
loggingtimestamp
loggingbuffereddebugging
icmppermitanyinside
mtuoutside1500
mtuinside1500
---IPaddressesontheinterfaces
ipaddressoutside172.18.124.96255.255.255.0
ipaddressinside10.0.25.254255.255.255.0
ipauditinfoactionalarm
ipauditattackactionalarm
pdmlogginginformational100
pdmhistoryenable
arptimeout14400
global(outside)1interface
---BypassofNATforIPSecinterestinginsidenetworktraffic
nat(inside)0access-listnonat
nat(inside)10.0.0.00.0.0.000
---DefaultgatewaytotheInternet
routeoutside0.0.0.00.0.0.0172.18.124.11
timeoutxlate0:
05:
00
timeoutconn1:
00:
00half-closed0:
10:
00udp0:
02:
00rpc0:
00h2251:
timeouth3230:
00mgcp0:
00sip0:
30:
00sip_media0:
timeoutuauth0:
00absolute
aaa-serverTACACS+protocoltacacs+
aaa-serverRADIUSprotocolradius
aaa-serverLOCALprotocollocal
http10.0.0.0255.0.0.0inside
nosnmp-serverlocation
nosnmp-servercontact
snmp-servercommunitypublic
nosnmp-serverenabletraps
floodguardenable
---ThiscommandavoidsappliedACLsorconduitsonencryptedpackets
sysoptconnectionpermit-ipsec
---ConfigurationofIPSecPhase2
cryptoipsectransform-setmytransesp-3desesp-sha-hmac
cryptomapmymap10ipsec-isakmp
cryptomapmymap10matchaddressnonat
cryptomapmymap10setpfsgroup2
cryptomapmymap10setpeer172.18.173.85
cryptomapmymap10settransform-setmytrans
cryptomapmymapinterfaceoutside
---ConfigurationofIPSecPhase1
isakmpenableoutside
---InternetKeyExchange(IKE)pre-sharedkey
---thatthepeerswillusetoauthenticate
isakmpkeytestmeaddress172.18.173.85netmask255.255.255.255
isakmpidentityaddress
isakmppolicy10authenticationpre-share
isakmppolicy10encryption3des
isakmppolicy10hashsha
isakmppolicy10group2
isakmppolicy10lifetime86400
telnettimeout5
sshtimeout5
consoletimeout0
dhcpdlease3600
dhcpdping_timeout750
terminalwidth80
配置NetScreen防火墙
FollowthestepsbelowtoconfiguretheNetScreenFirewall.
GotoLists>
Address,clicktheTrustedtab,andclickNewAddress.
AddtheNetscreeninternalnetworkthatwillbeencryptedonthetunnel,thenclickOK.
Note:
EnsurethattheTrustoptionisselected.
Theexamplebelowusesnetwork10.0.3.0withamaskof255.255.255.0.
Address,clicktheUntrustedtab,andclickNewAddress.
AddtheremotenetworkthatNetScreenFirewallwillusewhenencryptingpackets,thenclickOK.
Theexamplebelowusesnetwork10.0.25.0withamaskof255.255.255.0.
ToconfiguretheVPNgateway(Phase1andPhase2IPSecpolicies),gotoNetwork>
VPN,selecttheGatewaytab,andclickNewRemoteTunnelGateway.
UsetheIPaddressofthePIX'
soutsideinterfacetoterminatethetunnel,andconfigurethePhase1IKEoptionstobind.ClickOKwhenyouarefinished.
Thisexampleusesthefollowingfieldsandvalues.
GatewayName:
To501
StaticIPAddress:
172.18.124.96
Mode:
Main(IDProtection)
PresharedKey:
“testme”
Phase1proposal:
pre-g2-3des-sha
Whenyouhavesuccessfullycreatedtheremotetunnelgateway,youshouldseeascreensimilartothefollowingexample.
ToconfigureProposal1,selecttheP1Proposaltab,andthenclickNewPhase1Proposal.
EntertheconfigurationinformationforthePhase1Proposal,andthenclickOK.
ThisexampleusesthefollowingfieldsandvaluesPhase1exchange.
Name:
ToPix501
Authentication:
Preshare
DHGroup:
Group2
Encryption:
3DES-CBC
Hash:
SHA-1
Lifetime:
3600Sec.
WhenyouhavesuccessfullyaddedPhase1totheNetScreenconfiguration,youshouldseeascreensimilartothefollowingexample.
ToconfigurePhase2,selecttheP2Proposaltab,andthenclickNewPhase2Proposal.
EntertheconfigurationinformationforthePhase2Proposal,andthenclickOK.
ThisexampleusesthefollowingfieldsandvaluesforPhase2exchange.
PerfectForwardSecrecy:
DH-2(1024bits)
EncryptionAlgorithm:
AuthenticationAlgorithm:
26400Sec
WhenyouhavesuccessfullyaddedPhase2totheNetScreenconfiguration,youshouldseeascreensimilartothefollowingexample.
TocreateandconfigureAutoKeysIKE,selecttheAutoKeyIKEtab,andthenclickNewAutoKeyIKEEntry.
EntertheconfigurationinformationforAutoKeyIKE,andthenclickOK.
ThisexampleusesthefollowingfieldsandvaluesforAutoKeyIKE.
VPN-1
RemoteGatewayTunnelName:
(ThiswaspreviouslycreatedontheGatewaytab.)
Phase2Proposal:
(ThiswaspreviouslycreatedontheP2Proposaltab.)
VPNMonitor:
Enable
(ThisenablestheNetScreendevicetosetSimpleNetworkManagementProtocol[SNMP]trapstomonitortheconditionoftheVPNMonitor.)
WhenyouhavesuccessfullyconfiguredtheVPN-1rule,youshouldseeascreensimilartothefollowingexample.
ToconfiguretherulesthatallowencryptionoftheIPSectraffic,gotoNetwork>
Policy,selecttheOutgoingtab,andclickNewPolicy.
Entertheconfigurationinformationforthepolicy,andthenclickOK.
Thisexampleusesthefollowingfieldsandvaluesforthepolicy.TheNamefieldisoptionalandisnotusedinthisexample.
SourceAddress:
InsideNetwork
(ThiswaspreviouslydefinedontheTrustedtab.)
DestinationAddress:
RemoteNetwork
(ThiswaspreviouslydefinedundertheUntrustedtab.)
Service:
Any
Action:
Tunnel
VPNTunnel:
(ThiswaspreviouslydefinedastheVPNtunnelontheAutoKeyIKEtab.)
ModifymatchingincomingVPNpolicy:
Checked
(ThisoptionautomaticallycreatesaninboundrulethatmatchestheoutsidenetworkVPNtraffic.)
Whenyouhaveaddedthepolicy,ensurethattheoutboundVPNruleisfirstinthelistofpolicies.(TherulethatwascreatedautomaticallyforinboundtrafficisontheIncomingtab.)
Ifyouneedtochangetheorderofthepolicies,followthesesteps.
ClicktheOutgoingtab.
ClickthecirculararrowsintheConfigurecolumntodisplaytheMovePolicyMicrowindow.
ChangetheorderofthepoliciessothattheVPNpolicyisabovepolicyID0(sothattheVPNpolicyisatthetopofthelist).
YoucanviewtheruleforinboundtrafficbyclickingontheIncomingtab.
验证配置
ping-Diagnosesbasicnetworkconnectivity.
showcryptoipsecsa-ShowsthePhase2securityassociations.
showcryptoisakmpsa-ShowsthePhase1securityassociations.
验证示例
Sampleoutputfrompingandshowcommandsisshowbelow.
ThispingwasinitiatedfromahostbehindtheNetScreenFirewall.
C:
\>
ping10.0.25.1-t
Requesttimedout.
Replyfrom10.0.25.1:
bytes=32time<
105msTTL=128
114msTTL=128
106msTTL=128
121msTTL=128
110msTTL=128
116msTTL=128
109msTTL=128
118msTTL=128
Outputfromtheshowcryptoipsecsacommandisshownbelow.
pixfirewall(config)#showcryptoipsecsa
interface:
outside
Cryptomaptag:
mymap,localaddr.172.18.124.96
localident(addr/mask/prot/port):
(10.0.25.0/255.255.255.0/0/0)
remoteident(addr/mask/prot/port):
(10.0.3.0/255.255.255.0/0/0)
current_peer:
172.18.173.85:
500
PERMIT,flags={origin_is_acl,}
#pktsencaps:
11,#pktsencrypt:
11,#pktsdigest11
#pktsdecaps:
11,#pktsdecrypt:
13,#pktsverify13
#pktscompressed:
0,#pktsdecompressed:
0
#pktsnotcompressed:
0,#pktscompr.failed:
0,
#pktsdecompressfailed:
0,#senderrors0,#recverrors1
localcryptoendpt.:
172.18.124.96,
remotecryptoendpt.:
172.18.173.85
pathmtu1500,ipsecoverhead56,mediamtu1500
currentoutboundspi:
f0f376eb
inboundespsas:
spi:
0x1225ce5c(304467548)
transform:
esp-3desesp-sha-hmac,
inusesettings={Tunnel,}
slot:
0,connid:
3,cryptomap:
mymap
satiming:
remainingkeylifetime(k/sec):
(4607974/24637)
IVsize:
8bytes
replaydetectionsupport:
Y
inboundahsas:
inboundpcpsas:
outboundespsas:
0xf0f376eb(4042487531)
4,cryptomap:
(4607999/24628)
outboundahsas:
outboundpcpsas:
Outputfromtheshowcryptoisakmpsacommandisshownbelow.
pixfirewall(config)#showcryptoisakmpsa
Total:
1
Embryonic:
dstsrcstatependingcreated
172.18.124.96172.18.173.85QM_IDLE01
Troubleshoot
Thissectionprovidesinformationyoucanusetotroubleshootyourconfiguration.
调试命令
debugcryptoengine-Displaysmessagesaboutcryptoengines.
debugcryptoipsec-DisplaysinformationaboutIPSecevents.
debugcrypto
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- LAN TO VPN
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 广东省普通高中学业水平考试数学科考试大纲Word文档下载推荐.docx
广东省普通高中学业水平考试数学科考试大纲Word文档下载推荐.docx
