 IPSecVPN高可用Word文档格式.docx
IPSecVPN高可用Word文档格式.docx
- 文档编号:21216714
- 上传时间:2023-01-28
- 格式:DOCX
- 页数:18
- 大小:208.56KB
IPSecVPN高可用Word文档格式.docx
《IPSecVPN高可用Word文档格式.docx》由会员分享,可在线阅读,更多相关《IPSecVPN高可用Word文档格式.docx(18页珍藏版)》请在冰豆网上搜索。
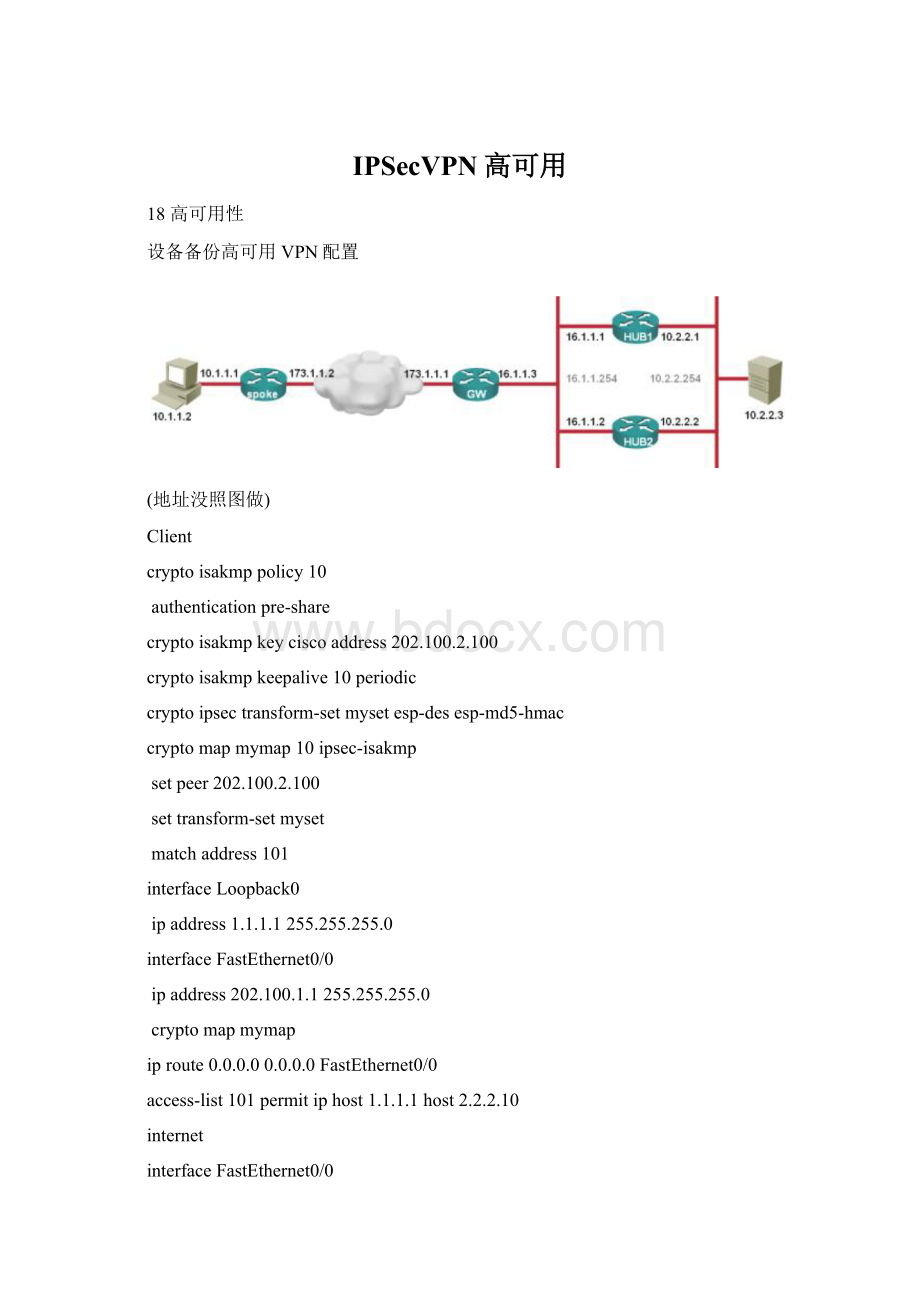
interfaceFastEthernet0/0
ipaddress202.100.1.1255.255.255.0
cryptomapmymap
iproute0.0.0.00.0.0.0FastEthernet0/0
access-list101permitiphost1.1.1.1host2.2.2.10
internet
ipaddress202.100.1.10255.255.255.0
interfaceFastEthernet1/0
ipaddress202.100.2.10255.255.255.0
__________________________________________________________________
active
cryptoisakmpkeyciscoaddress202.100.1.1
setpeer202.100.1.1
reverse-routetag10
reverse-routestatic——当IPsec感知到本设备是active的HSRP状态,那么即使没有SA也会注入感兴趣流路由使得本地内部可以先发起流量
ipaddress202.100.2.1255.255.255.0
standby1ip202.100.2.100
standby1priority105
standby1preempt
standby1namehsrp
cryptomapmymapredundancyhsrp——让IPsec感知HSRP路由器的激活和备份状态
ipaddress2.2.2.1255.255.255.0
routerospf1
redistributestaticsubnetsroute-maps2o
network2.2.2.00.0.0.255area0
access-list101permitiphost2.2.2.10host1.1.1.1
route-maps2opermit10
matchtag10
standby
reverse-routestatic————因为本地是standby,即使打了这个命令也不会注入路由
ipaddress202.100.2.2255.255.255.0
cryptomapmymapredundancyhsrp
ipaddress2.2.2.2255.255.255.0
inside
ipaddress2.2.2.10255.255.255.0
链路备份也叫RedundancyVPN,是一种常见的解决方案,支持双方首先发起流量并且支持抢占功能
链路备份高可用VPN配置
缺点:
没有抢占功能,必须R1端先发起流量,由于没有HSRP所以IPsec不能打reverse-routestatic
client
cryptoisakmpkeyciscoaddress202.100.1.2
cryptoisakmpkeyciscoaddress61.128.128.3
setpeer202.100.1.2
setpeer61.128.128.3
ipaddress10.1.1.1255.255.255.0
access-list101permitiphost1.1.1.1host2.2.2.4
ipaddress10.1.1.5255.255.255.0
ipaddress202.100.1.5255.255.255.0
interfaceFastEthernet2/0
ipaddress61.128.128.5255.255.255.0
cryptoisakmpkeyciscoaddress0.0.0.00.0.0.0
cryptodynamic-mapdymap10
cryptomapmymap1000ipsec-isakmpdynamicdymap
ipaddress202.100.1.2255.255.255.0
redistributestaticmetric1subnetsroute-maps2o
network2.2.2.20.0.0.0area0
ipaddress61.128.128.3255.255.255.0
ipaddress2.2.2.3255.255.255.0
network2.2.2.30.0.0.0area0
ipaddress2.2.2.4255.255.255.0
network2.2.2.40.0.0.0area0
回环建立VPN
R1
cryptoisakmpkey0ciscoaddress3.3.3.3
setpeer3.3.3.3
ipaddress12.12.12.1255.255.255.0
noshutdown
access-list101permitip10.1.1.00.0.0.25530.1.1.00.0.0.255
R2
ipaddress12.12.12.2255.255.255.0
noshutdown
interfaceEthernet1/0
ipaddress23.23.23.2255.255.255.0
interfaceEthernet1/1
ipaddress32.32.32.2255.255.255.0
iproute3.3.3.3255.255.255.25523.23.23.3
iproute3.3.3.3255.255.255.25532.32.32.3
R3
cryptoisakmpkey0ciscoaddress12.12.12.1
cryptomapmymaplocal-addressLoopback1
setpeer12.12.12.1
ipaddress30.1.1.1255.255.255.0
interfaceLoopback1
ipaddress3.3.3.3255.255.255.255
interfaceEthernet0/0
ipaddress23.23.23.3255.255.255.0
noshu
interfaceEthernet0/1
ipaddress32.32.32.3255.255.255.0
iproute0.0.0.00.0.0.023.23.23.2
iproute0.0.0.00.0.0.032.32.32.2
access-list101permitip30.1.1.00.0.0.25510.1.1.00.0.0.255
好处:
IPSecSA被复制到了crymap的所有接口,并且同IKE关联起来,链接状态在所有接口之间共享,从而节省了内存和处理资源,恢复速度和IPSec对等体间的路由选择协议收敛一样快,
测试:
R1#ping30.1.1.1source10.1.1.1
!
Router#showcryptoipsecsa
interface:
Ethernet0/0
inboundespsas:
spi:
0xA67C531D(2793165597)
outboundespsas:
0xD2A5C98C(3534080396)
Ethernet0/1
R1#ping30.1.1.1source10.1.1.1repeat10000
...............!
Successrateis88percent
PPPMLVPN
hostnameR1
cryptoisakmpkeyciscoaddress23.1.1.3
setpeer23.1.1.3
hostnameR2
interfaceMultilink1
ipaddress23.1.1.2255.255.255.0
pppmultilink
pppmultilinkgroup1
interfaceSerial2/0
noipaddress
encapsulationppp
serialrestart-delay0
interfaceSerial2/1
hostnameR3
cryptoisakmpkeyciscoaddress12.12.12.1
ipaddress23.1.1.3255.255.255.0
interfaceSerial1/0
interfaceSerial1/1
iproute0.0.0.00.0.0.0Multilink1
测试
高可用测试
Router#ping30.1.1.1source10.1.1.1repeat1000
..........!
.
Successrateis65percent(21/32)
双隧道路由方式
encr3des
hashmd5
group2
cryptoisakmpkeyciscoaddress24.1.1.4
cryptoipsecprofilemypro
interfaceTunnel0
ipaddress13.1.1.1255.255.255.0
t
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- IPSecVPN 可用
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 对中国城市家庭的教育投资行为的理论和实证研究.docx
对中国城市家庭的教育投资行为的理论和实证研究.docx
