 IPSECVPNWord文档下载推荐.docx
IPSECVPNWord文档下载推荐.docx
- 文档编号:18641412
- 上传时间:2022-12-30
- 格式:DOCX
- 页数:13
- 大小:35.39KB
IPSECVPNWord文档下载推荐.docx
《IPSECVPNWord文档下载推荐.docx》由会员分享,可在线阅读,更多相关《IPSECVPNWord文档下载推荐.docx(13页珍藏版)》请在冰豆网上搜索。
1.1.4、VPN配制
R1=================================================
access-list101permitiphost10.1.1.1host10.2.2.1
cryptoisakmppolicy1
authenticationpre-share
hashmd5
cryptoisakmpkey0ciscoaddress200.200.100.2255.255.255.0
cryptoipsectransform-setshanghaiesp-desesp-md5-hmac
cryptomapvpn_to_shanghai10ipsec-isakmp
matchadd101
setpeer200.200.100.2
settransformshanghai
iproute10.2.2.0255.255.255.0200.200.100.2
cryptomapvpn_to_shanghai
R2================================================
access-list101permitiphost10.2.2.1host10.1.1.1
exit
cryptoisakmpkey0ciscoaddress200.200.100.1255.255.255.0
setpeer200.200.100.1
iproute10.1.1.0255.255.255.0200.200.100.1
1.1.5、校验
在R1上扩展ping
10.2.2.1
R1#ping
Protocol[ip]:
TargetIPaddress:
Repeatcount[5]:
Datagramsize[100]:
Timeoutinseconds[2]:
Extendedcommands[n]:
y
Sourceaddressorinterface:
loo0
Typeofservice[0]:
SetDFbitinIPheader?
[no]:
Validatereplydata?
Datapattern[0xABCD]:
Loose,Strict,Record,Timestamp,Verbose[none]:
Sweeprangeofsizes[n]:
Typeescapesequencetoabort.
Sending5,100-byteICMPEchosto10.2.2.1,timeoutis2seconds:
Packetsentwithasourceaddressof10.1.1.1
..!
Successrateis60percent(3/5),round-tripmin/avg/max=172/238/288ms
R1#showcryptomap
CryptoMap"
vpn_to_shanghai"
10ipsec-isakmp
Peer=200.200.100.2
ExtendedIPaccesslist101
access-list101permitiphost10.1.1.1host10.2.2.1
Currentpeer:
200.200.100.2
Securityassociationlifetime:
4608000kilobytes/3600seconds
PFS(Y/N):
N
Transformsets={
shanghai,
}
Interfacesusingcryptomapvpn_to_shanghai:
Serial1/1
R1#showcryptoipsecsa
interface:
Cryptomaptag:
vpn_to_shanghai,localaddr200.200.100.1
protectedvrf:
(none)
local
ident(addr/mask/prot/port):
(10.1.1.1/255.255.255.255/0/0)
remoteident(addr/mask/prot/port):
(10.2.2.1/255.255.255.255/0/0)
current_peer200.200.100.2port500
PERMIT,flags={origin_is_acl,}
#pktsencaps:
3,#pktsencrypt:
3,#pktsdigest:
3
#pktsdecaps:
3,#pktsdecrypt:
3,#pktsverify:
#pktscompressed:
0,#pktsdecompressed:
0
#pktsnotcompressed:
0,#pktscompr.failed:
#pktsnotdecompressed:
0,#pktsdecompressfailed:
#senderrors2,#recverrors0
localcryptoendpt.:
200.200.100.1,remotecryptoendpt.:
pathmtu1500,ipmtu1500
currentoutboundspi:
0xC57F1ABD(3313441469)
inboundespsas:
spi:
0x9C8542B5(2625979061)
transform:
esp-desesp-md5-hmac,
inusesettings={Tunnel,}
connid:
2001,flow_id:
SW:
1,cryptomap:
vpn_to_shanghai
satiming:
remainingkeylifetime(k/sec):
(4416419/3493)
IVsize:
8bytes
replaydetectionsupport:
Y
Status:
ACTIVE
inboundahsas:
inboundpcpsas:
outboundespsas:
2002,flow_id:
2,cryptomap:
(4416419/3492)
outboundahsas:
outboundpcpsas:
R1#showcryptoisakmpsa
QOS
一、描述
QOS:
策略设置,一般分为几个步骤
第一:
分类流量
1.1.1、根据IP地址分类,配制的时候使用ACL访问控制列表
1.1.2、根据思科NBAR[nba:
]来分类,它可以根据七层来识别
Router(config)#class-mapmap名
Router(config-cmap)#match
?
access-group
Access
group
any
Any
packets
class-map
Class
map
cos
IEEE
802.1Q/ISL
class
of
service/user
priority
values
destination-address
Destination
address
input-interface
Select
an
input
interface
to
match
ip
IP
specific
mpls
Multi
Protocol
Label
Switching
not
Negate
this
match
result
protocol
/NBAR
qos-group
Qos-group
source-address
Source
第二:
标记流量(marking)
标记可以基于二层ip
precedenc(IP优先级)也可以基于三层DSCP来标记识别的流量
一般在标记的时候分为几大块:
语音流、视频流、重要业务流、其它业务流分为从0-7这么几个级别
7和6保留0也保留
级别
流量种类
dscp标记
实例
5
语音
ef
voip
4
流媒体
af4x
视频会议等
3
业务流量
af3x
ERP、SQL等办公系统
2
传统流量
af2x
mail、ftp、web等
1
垃圾流量
af1x
抢占带宽的流量例:
bt,迅雷,ppstream等
注:
x代表(1-9)是同一个级别内在分类
设置
policy-map
名称
class-map
set
dscp
{DSCP}
set
precedence
{PRECEDENCE}
{COS}
设置标记
第三:
设置策略
在policy-map下,匹配class-map后
{Kbps|percent
PERCENT}
[bc]
定义优先级流量的带宽以及突发流量
bandwidth
定义保留带宽
random-detect
启用WRED
police
{CIR
BC
BE}
conform-action
{action}
exceed-action
[violated-action
{action}]
使用令牌桶限速
queue-limit
{PACKETS}
定义队列中数据报的最大个数
service-policy
{policy-name}
调用其它的策略进行嵌套
shape
{average|peak}
[BC]
[BE]}
整形
drop
丢弃
第四:
在接口上应用
Router(config-if)#service-policy
{input|output}
{policy_map名字}
input
设置在进口上
output
设置在出口上
如果对QOS不太懂建议看
是一个哥儿们写的笔记很不错
二、拓扑
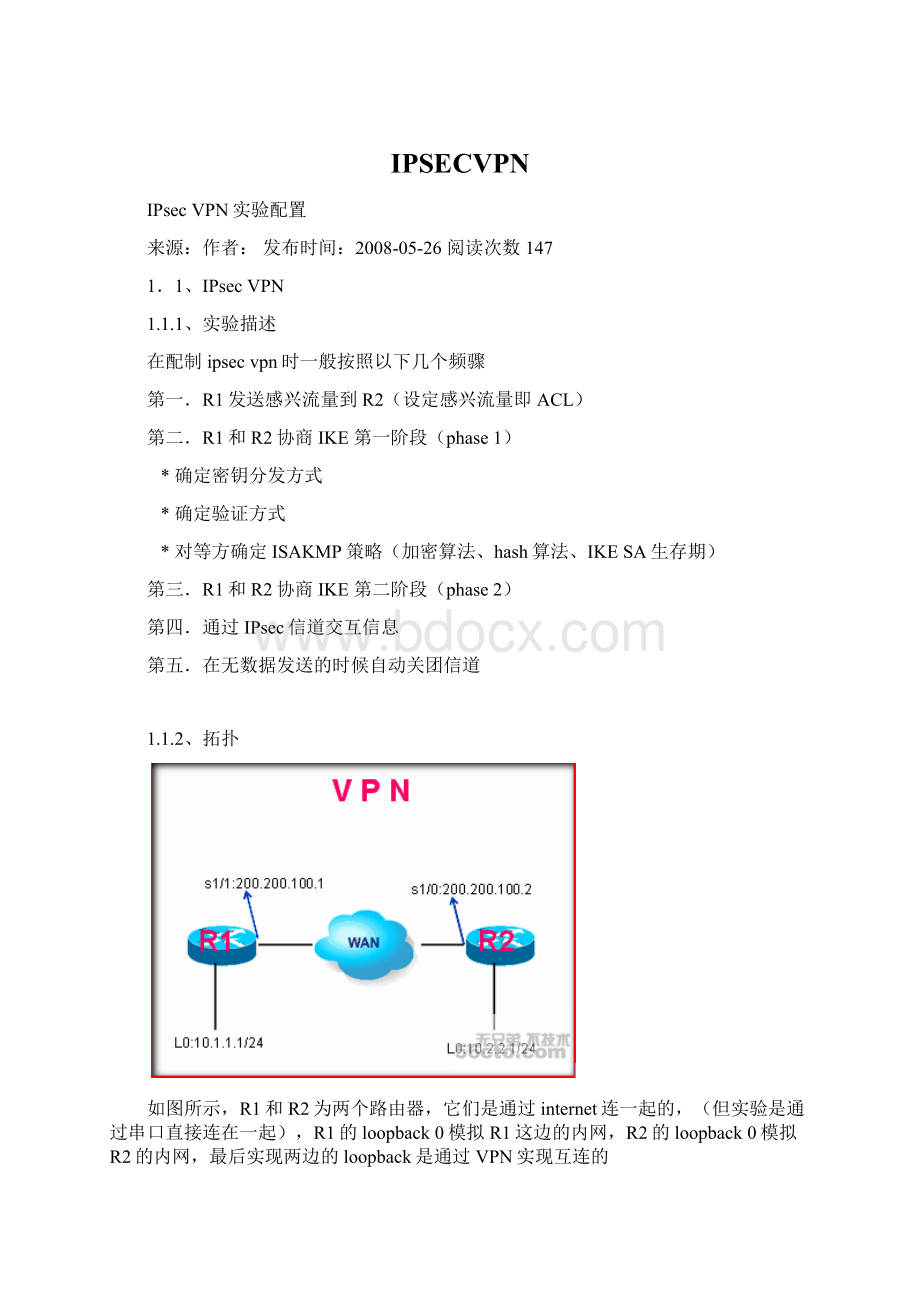
图中,COM路由器接内网,ISP路由器是模拟的外网,R2属于边界路由器
三、实验说明
我们在R2的s1/0和s1/1口上配制接口带宽为16Kbit/s,然后在s1/0即进口上做标记,
标记为,满足条件打20的标记,超出的打10的标记。
在s1/1出口上做策略对于打了10标记的流量,做相应的drop
四、配制
基本配制
R1:
interfaceSerial1/1
ipaddress10.1.1.2255.255.255.0
nosh
iproute20.1.1.0255.255.255.010.1.1.1
R2:
access-list100permitip10.1.1.00.0.0.25520.1.1.00.0.0.255
16000为带宽限制,2000为BC,3000为BE
class-mapin-put
matchaccess-group100
policy-mapin-put
classin-put
police1600020003000conform-actionset-dscp-transmit20exceed-actionset-dscp-transmit10
class-mapout-put
对于超出的流量做drop
matchipdscp10
policy-mapout-put
classout-put
police800015003000conform-actiontransmitexceed-actiondrop
bandwidth16
ipaddress10.1.1.1255.255.255.0
clockrate64000
service-policyinputin-put
ipaddress20.1.1.1255.255.255.0
service-policyoutputout-put
R3:
interfaceSerial1/0
ipaddress20.1.1.2255.255.255.0
iproute10.1.1.0255.255.255.020.1.1.1
验证
R1#pingip
20.1.1.2
10
2000
Sending10,2000-byteICMPEchosto20.1.1.2,timeoutis2seconds:
.!
Successrateis60percent(6/10),round-tripmin/avg/max=204/457/596ms
R2#showpolicy-map
PolicyMapout-put
Classout-put
policecir8000bc1500be3000
conform-actiontransmit
exceed-actiondrop
PolicyMapin-put
Classin-put
policecir16000bc2000be3000
conform-actionset-dscp-transmitaf22
exceed-actionset-dscp-transmitaf11
从showpolicy-map我们就可以知道,我们先前设置的
police1600020003000conform-actionset-dscp-transmit20exceed-actionset-dscp-transmit10
police800015003000conform-actiontransmitexceed-actiondrop
语名的意义16000是CAR承诺接入速率其中bc是令牌桶be是当信令在bc放满后放到be中
R2#showpolicy-mapints1/0
Serial1/0
Class-map:
in-put(match-all)
405packets,460260bytes
5minuteofferedrate1000bps,droprate0bps
Match:
access-group100
police:
cir16000bps,bc2000bytes
conformed175packets,137072bytes;
actions:
set-dscp-transmitaf22
exceeded230packets,323188bytes;
set-dscp-transmitaf11
conformed1000bps,exceed0bps
class-default(match-any)
0packets,0bytes
5minuteofferedrate0bps,droprate0bps
any
R2#showpolicy-mapints1/1
Serial1/1
out-put(match-all)
165packets,231820bytes
ipdscpaf11(10)
cir8000bps,bc1500bytes
conformed88packets,117892bytes;
transmit
exceeded77packets,113928bytes;
drop
conformed0bps,exceed0bps
261packets,122786bytes
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- IPSECVPN
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 铝散热器项目年度预算报告.docx
铝散热器项目年度预算报告.docx
