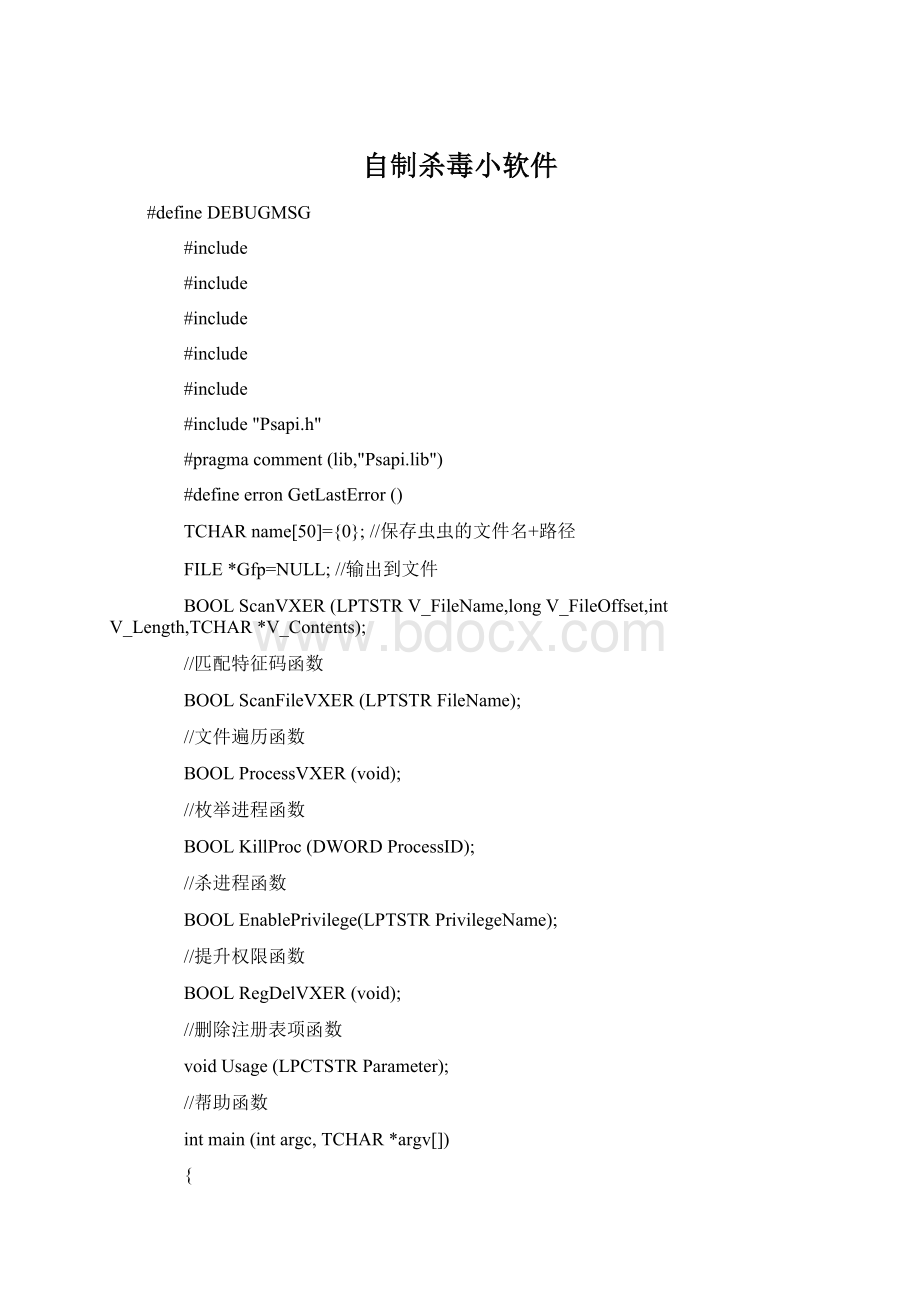
 自制杀毒小软件Word格式文档下载.docx
自制杀毒小软件Word格式文档下载.docx
- 文档编号:18390513
- 上传时间:2022-12-15
- 格式:DOCX
- 页数:15
- 大小:18.14KB
自制杀毒小软件Word格式文档下载.docx
《自制杀毒小软件Word格式文档下载.docx》由会员分享,可在线阅读,更多相关《自制杀毒小软件Word格式文档下载.docx(15页珍藏版)》请在冰豆网上搜索。
{
if(argc!
=2)
Usage(argv[0]);
return0;
}
#ifdefDEBUGMSG
Gfp=fopen("
VXER.txt"
"
a+"
);
if(Gfp==NULL)
printf("
Open\"
VXER.txt\"
fail\n"
fprintf(Gfp,"
%s\n\n"
[-------------------------Filelist-------------------------]"
#endif
if(strlen(argv[1])>
10)
Finenamenolargerthan\"
10\"
\n"
if(!
(ScanFileVXER(argv[1])))
ScanFileVXER()GetLastErrorreports%d\n"
erron);
fclose(Gfp);
(ProcessVXER()))
ProcessesVXER()GetLastErrorreports%d\n"
(RegDelVXER()))
RegDelVXER()GetLastErrorreports%d\n"
BOOLScanFileVXER(LPTSTRFileName)
WIN32_FIND_DATAFindFileData;
DWORDlpBufferLength=255;
TCHARlpBuffer[255]={0};
TCHARDirBuffer[255]={0};
HANDLEhFind=NULL;
UINTcount=0;
longFileOffset=0x1784;
//偏移地址
intFileLength=0x77;
//长度
TCHARContents[]={
0x49,0x20,0x6A,0x75,0x73,0x74,0x20,0x77,0x61,0x6E,0x74,0x20,0x74,0x6F,0x20,0x73,
0x61,0x79,0x20,0x4C,0x4F,0x56,0x45,0x20,0x59,0x4F,0x55,0x20,0x53,0x41,0x4E,0x21,
0x21,0x20,0x62,0x69,0x6C,0x6C,0x79,0x20,0x67,0x61,0x74,0x65,0x73,0x20,0x77,0x68,
0x79,0x20,0x64,0x6F,0x20,0x79,0x6F,0x75,0x20,0x6D,0x61,0x6B,0x65,0x20,0x74,0x68,
0x69,0x73,0x20,0x70,0x6F,0x73,0x73,0x69,0x62,0x6C,0x65,0x20,0x3F,0x20,0x53,0x74,
0x6F,0x70,0x20,0x6D,0x61,0x6B,0x69,0x6E,0x67,0x20,0x6D,0x6F,0x6E,0x65,0x79,0x20,
0x61,0x6E,0x64,0x20,0x66,0x69,0x78,0x20,0x79,0x6F,0x75,0x72,0x20,0x73,0x6F,0x66,
0x74,0x77,0x61,0x72,0x65,0x21,0x21};
//从冲击波中提取出来的,用做特征码
//获取系统目录的完整路径
if(GetSystemDirectory(DirBuffer,lpBufferLength)!
=0)
if(SetCurrentDirectory(DirBuffer)!
=0)//设置为当前目录
hFind=FindFirstFile(FileName,&
FindFileData);
//查找文件
if(hFind==INVALID_HANDLE_VALUE)
FindFirstFile()GetLastErrorreports%d\n"
if(hFind!
=NULL)
FindClose(hFind);
returnFALSE;
else
count++;
//获得文件的完整路径
if(GetFullPathName(FindFileData.cFileName,lpBufferLength,lpBuffer,NULL)!
File:
\t\t%s\n"
lpBuffer);
#else
GetFullPathName()GetLastErrorreports%d\n"
//进行特征码匹配工作
ScanVXER(FindFileData.cFileName,FileOffset,FileLength,Contents);
while(FindNextFile(hFind,&
FindFileData))//继续查找文件
//以"
."
和"
.."
除外
if(strcmp("
FindFileData.cFileName)==0||strcmp("
FindFileData.cFileName)==0)
Filenoinclude\"
.\"
and\"
..\"
exit(0);
NextFile:
\t%s\n"
\nFileTotal:
%d\n\n"
count);
[-------------------------Fileend---------------------------]\n"
FileTotal:
%d\n"
//打印出查找到的文件各数
//关闭搜索句柄
returnTRUE;
BOOLScanVXER(
LPTSTRV_FileName,//文件名
longV_FileOffset,//偏移地址
intV_Length,//长度
TCHAR*V_Contents)//具体内容
TCHARFileContents[255]={0};
intcmpreturn=0;
FILE*fp=NULL;
fp=fopen(V_FileName,"
rb"
//以二进制只读方式打开
if(fp==NULL)
fopen()FileopenFAIL\n"
fclose(fp);
fseek(fp,V_FileOffset,SEEK_SET);
//把文件指针指向特征码在文件的偏移地址处
fread(FileContents,V_Length,1,fp);
//读取长度为特征码长度的内容
cmpreturn=memcmp(V_Contents,FileContents,V_Length);
//进行特征码匹配。
失败返回FALSE
if(cmpreturn==0)
Filematchcompletely\n"
//打印文件匹配消息
strcpy(name,V_FileName);
//将文件名保存在全局变量name中
if(fp!
BOOLProcessVXER(void)
DWORDlpidProcess[1024]={0};
DWORDcbNeeded_1,cbNeeded_2;
HANDLEhProc=NULL;
HMODULEhMod[1024]={0};
TCHARProcFile[MAX_PATH];
TCHARFileName[50]={0};
UINTPcount=0;
inti=0;
EnablePrivilege(SE_DEBUG_NAME);
//提升调试进程权限
[------------------------Processlist--------------------------]"
strcpy(FileName,"
C:
\\WINNT\\system32\\"
strcat(FileName,name);
//把文件名+路径复制到FileName变量中
//枚举进程
(EnumProcesses(lpidProcess,sizeof(lpidProcess),&
cbNeeded_1)))
EnumProcesses()GetLastErrorreports%d\n"
if(hProc!
CloseHandle(hProc);
for(i=0;
i<
(int)cbNeeded_1/4;
i++)
//打开找到的第一个进程
hProc=OpenProcess(PROCESS_ALL_ACCESS,FALSE,lpidProcess);
if(hProc)
//枚举进程模块
if(EnumProcessModules(hProc,hMod,sizeof(hMod),&
cbNeeded_2))
//枚举进程模块文件名,包含全路径
if(GetModuleFileNameEx(hProc,hMod[0],ProcFile,sizeof(ProcFile)))
[%5d]\t%s\n"
lpidProcess,ProcFile);
//输出进程
//可以考虑将其注释掉,这样就不会输出进程列表了
Pcount++;
//查找进程中是否包含FileName
if(strcmp(FileName,ProcFile)==0)
//如果包含,则杀掉。
KillProc为自定义的杀进程函数
(KillProc(lpidProcess)))
KillProc()GetLastErrorreports%d\n"
DeleteFile(FileName);
//进程杀掉后,再将文件删除
//关闭进程句柄
\nProcesstotal:
Pcount);
[------------------------Processend----------------------------]"
//打印进程各数
BOOLKillProc(DWORDProcessID)
//打开由ProcessVXER()传递的进程PID
hProc=OpenProcess(PROCESS_ALL_ACCESS,FALSE,ProcessID);
//终止进程
(TerminateProcess(hProc,0)))
TerminateProcess()GetLastErrorreports%d\n"
OpenProcess()GetLastErrorreports%d\n"
BOOLEnablePrivilege(LPTSTRPrivilegeName)
HANDLEhProc=NULL,hToken=NULL;
TOKEN_PRIVILEGESTP;
hProc=GetCurrentProcess();
//打开当前进程的一个伪句柄
//打开进程访问令牌,hToken表示新打开的访问令牌标识
if(!
OpenProcessToken(hProc,TOKEN_ADJUST_PRIVILEGES,&
hToken))
OpenProcessToken()GetLastErrorreports%d\n"
gotoClose;
//提升权限
LookupPrivilegeValue(NULL,PrivilegeName,&
TP.Privileges[0].Luid))
LookupPrivilegeValue()GetLastErrorreports%d\n"
TP.Privileges[0].Attributes=SE_PRIVILEGE_ENABLED;
TP.PrivilegeCount=1;
//允许权限,主要根据TP这个结构
AdjustTokenPrivileges(hToken,FALSE,&
TP,sizeof(TP),0,0))
AdjustTokenPrivileges()GetLastErrorreports%d\n"
Close:
if(hToken!
CloseHandle(hToken);
BOOLRegDelVXER(void)
HKEYhkey;
DWORDret=0;
//打开注册表的Run项
ret=RegOpenKeyEx(HKEY_LOCAL_MACHINE,
"
SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run\\"
0,
KEY_ALL_ACCESS,
&
hkey);
(ret==ERROR_SUCCESS))
RegOpenKeyEx()GetLastErrorreports%d\n"
//删除键值windowsautoupdate。
ret=RegDeleteValue(hkey,"
windowsautoupdate"
if(ret==ERROR_SUCCESS)
SuccessDelete\n"
RegDeleteValue()GetLastErrorreports%d\n"
RegCloseKey(hkey);
//exit(0);
//关闭打开的注册表项
voidUsage(LPCTSTRParameter)
LPCTSTRPath="
%SystemRoot%\\system32\\"
;
fprintf(stderr,"
============================================================================\n"
杀毒软件的简单实现\n"
环境:
Win2KAdvServer+VisualC++6.0\n"
作者:
laoxie\n"
主页:
OICQ:
77199033\n"
邮件:
dtzj@\n"
使用方法:
%s文件名。
例如:
%smsblast.exeor%s*.exe\n\n"
注
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- 自制 杀毒 软件
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 如何打造酒店企业文化2刘田江doc.docx
如何打造酒店企业文化2刘田江doc.docx
