 Application Systems IT Audit Program文档格式.docx
Application Systems IT Audit Program文档格式.docx
- 文档编号:17854669
- 上传时间:2022-12-11
- 格式:DOCX
- 页数:15
- 大小:20.60KB
Application Systems IT Audit Program文档格式.docx
《Application Systems IT Audit Program文档格式.docx》由会员分享,可在线阅读,更多相关《Application Systems IT Audit Program文档格式.docx(15页珍藏版)》请在冰豆网上搜索。
2.Inaccurateand/orcorrupteddatamayleadtoerroneousmanagementdecisions.
3.Thelackofwrittenprocedurescouldresultinafailuretocomplywithcorporatepoliciesandguidelines,aswellas,regulatoryagency(e.g.,FFIEC)requirements.
4.Businessapplicationsmaynotbeadequatelyprotectedfromunauthorizedaccessduetoineffectivesecurityprocedures.
5.Customerinformationmaybelost,manipulatedorstolen.
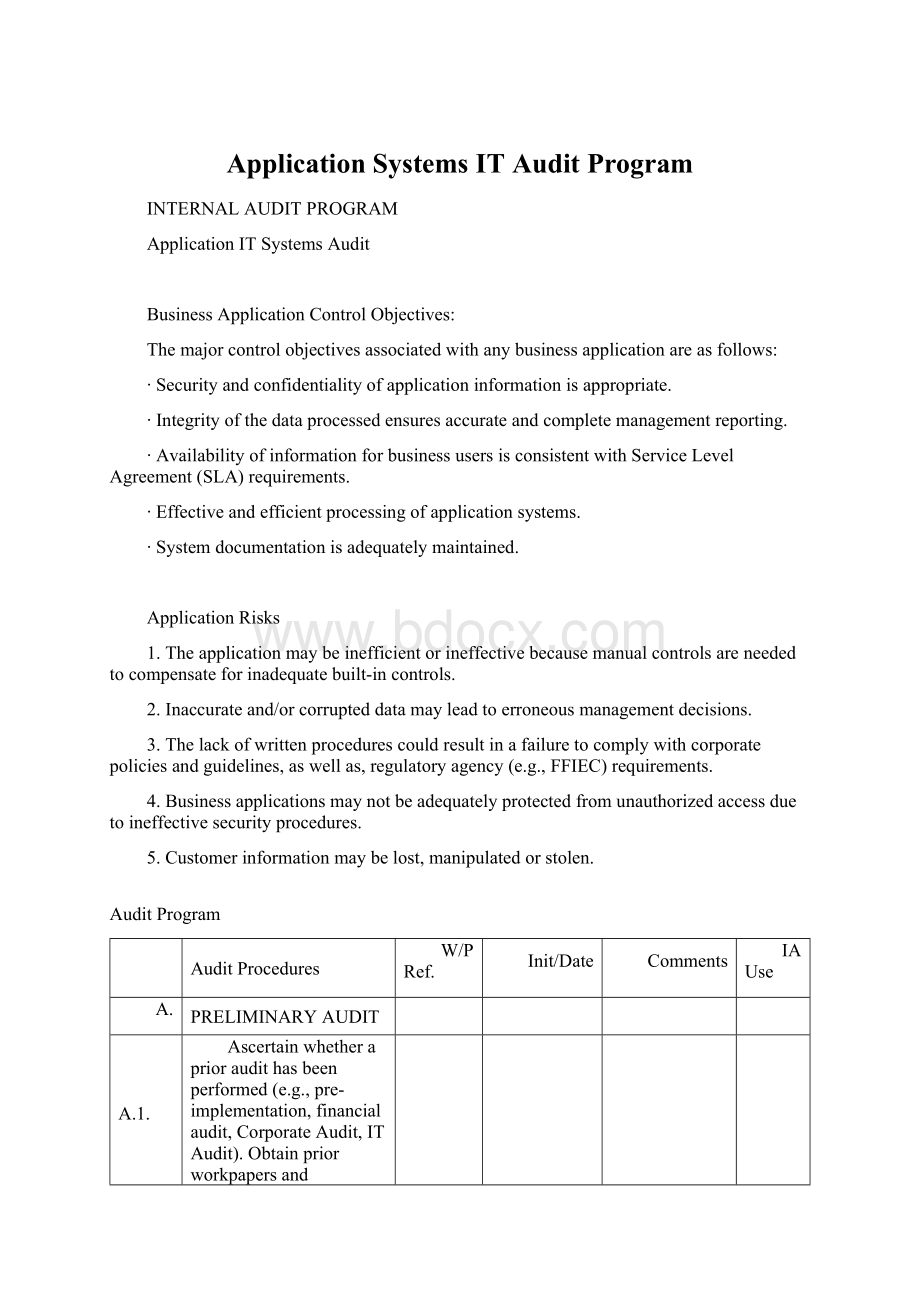
AuditProgram
AuditProcedures
W/PRef.
Init/Date
Comments
IAUse
A.
PRELIMINARYAUDIT
A.1.
Ascertainwhetheraprioraudithasbeenperformed(e.g.,pre-implementation,financialaudit,CorporateAudit,ITAudit).Obtainpriorworkpapersanddeterminewhatinformationcanbepulledforwardforthecurrentaudit.
A.2.
Ifaprioraudithasbeenperformed,obtainacopyoftheauditreport.Foreachauditissue/finding/controlweakness,performthefollowingsteps:
a.Obtainanddocumentthecurrentstatusofeachauditissue(includethenameoftheindividualsyoumet,dateoftheinterviews,andstatusofeachissue).
b.Notethedispositionofeachissue(Corrected/StillOpen).
c.Iftheissuestillexists,carryitforwardtothecurrentauditreport.Noteinthefollow-upworkpaperthatitwasbroughtforwardintothecurrentauditreport.
A.3.
Requestthefollowingdocumentationfromtheapplicationandoperationalmanagers:
∙ListofENSstaffandtheirresponsibilitiesformaintainingtheapplication.
∙ListofBusinessUnitsthatutilizefunctionsoroutputoftheapplication.
∙OrganizationChartsfromboththebusinessunitsthatutilizethesystemandtheENSstaff.
∙ListofMajorChangesmadetothisapplicationsincethelasttimeaudited.
∙ListofMajorChangesplannedtobemadetothisapplicationoverthenext12months.
∙CopyoftheApplicationSystemUserandSecurityManuals.Notethatthismaybeanonlinedocument.
∙CopyoftheSystemDocumentation(e.g.,overviewsystemflowcharts,systemnarratives)relatingtothisapplication.Notethismaybeanonlinedocument.
∙VendorContracts
∙CopyoftheUserSecurityAdministrationproceduresforthisapplication.
∙ServiceLevelAgreementfromENS.
∙Contingency/DisasterRecoveryPlansforthisapplication.
∙Backup,RestartandRecoveryPlanfromComputerOperations.
A.4.
Interviewtheapplicationandbusinessunitownerstogainanunderstandingofhowtheapplicationoperatesandidentifyanycriticalcontrolpoints,including:
a.Keyconcernsrelatingtothisapplicationsystem
b.Ownerrolesindefining,prioritizing,testingandapprovingsystemchanges
c.Participationonkeysystemprojects
Prepareabriefnarrativetodocumentyourunderstanding.
A.5.
ReviewtheVendorcontractsupportingtheapplication,ensuringthatthefollowingareasareaddressed:
a.[YourCo.]Responsibilities
b.VendorResponsibilities
c.Ownershipandlocationoftheapplication/sourcecode.
d.Release/upgradetestingandinstallationresponsibilities.
e.Maintenanceagreementsandterms
f.Ifaccessingourdata,privacyclauses.
g.SAS70
DocumenttheinclusionofthecontractinthecentralContractManagementSpreadsheetmaintainedbyENSinBowlingGreen.
B.
APPLICATIONCONTROLS
B.1.
ReviewsystemdocumentationobtainedfromthePreliminaryAuditStepstoverifythatitcontainsadescriptionof:
a.Transactiontypesprocessed
b.Systeminterfaces
c.Criticalprogramnamesandprocessingfunctions
d.Batchjobschedule(tasks)andcriticalprocessingperformed
e.SecurityAdministrationandaccesscontrolprocedures
B.2.
ObtainfromthePreliminaryAuditStepsordevelopanoverviewsystemflowchart/narrativeshowingmajorinputsources(e.g.,systemnames/filenames)andoutputtypes(e.g.,reportnames/systemnames/filenames/businessuserareas/ITareas).
INPUTCONTROLS
B.3.
ObtainfromthePreliminaryAuditStepsordevelopaflowofcriticalonlineinputtransactions.Identifythescreennamesandfunctiontypeswherethetransactionsareprocessed.
B.4.
Describetheeditandvalidationcontrolsforcriticalinputtransactions.Reviewinputscreenstoseethattheyaredesignedtopreventtheomissionofdataandtheacceptanceofinvaliddata.Ensurethatsignificantinputisverifiedbyanassociateotherthanthepersoninputtingthedata.
B.5.
Iftheapplicationusesbatchprocessing,determinethroughtestandobservationthatcontrolsoverinput(e.g.controltotals,reconciliations)areeffective.
PROCESSINGCONTROLS
B.6.
Reviewsystemdocumentationtodeterminethatkeycomputationsarefullydocumented.Testasampleofkeycomputationsusingamanualrecalculationprocess.
B.7.
Determineanddocumenttheprocesstoensurethatrejectedtransactionsarecorrectedandre-enteredpromptly,andthatcorrectedtransactionsaresubjecttothesameeditandbalancingcontrolsastheoriginaltransactions.
B.8.
Verifythatareconciliationprocessisperformeddailyforallinterfacesandanyoutstandingitemsareagedandresolvedtimely.Ensurethatthereconciliationactivitiesareadequatelyseparatedfrominputactivities.
B.9.
Determinethatrejecteditemsarelogged,tracked,aged,andresolvedtimely.Reviewrejectitemsreportstodeterminethat:
a.Reportsareproducedanddistributedtothebusinessuserarea.
b.Reportsevidencethattheyarerevieweddailybyappropriatebusinessuserstaff(e.g.,userinitialsandreviewdate).
c.Rejectsareresolvedaccuratelyandtimely(e.g.,requestrejectfollow-upprocedures).
OUTPUTCONTROLS
B.10.
Verifythatcontrolsareinplacetoensurethatoutputconfidentialityismaintained(whennecessary).Obtainalistofreportsindicatingtheirfrequency,purpose,andtheidentityoftherecipient.
B.11.
Reviewreportsproducedbytheapplication.Provideanopinionontheadequacyofthereportstosatisfytherequirementsofmanagement.TheserequirementsshouldhavebeengatheredinthePreliminaryAuditSteps.
B.12.
Determinethatareviewofcriticaltransactionsisperformed.Thisshouldbeperformedbysomeoneotherthanthepersonwhoinputdatafromthesourcedocuments.
C.
LOGICALACCESSCONTROLS
C.1.
ReviewtheUserSecurityAdministratorProcedurestoensurethat:
a.Proceduresareinplaceforissuing,approvingandmonitoringapplicationaccess.
b.Applicationaccessprocedurescomplywiththepolicyof“minimumaccess”.
c.Useraccesscontrolreportsareperiodicallyreviewedforaccuracyandcompletenessbyusermanagement.
C.2.
EnsurethatUserSecurityAdministrationproceduresaredefinedforthetimelydeletion/disablingofuserIds(e.g.,hires,terminations,changesinresponsibility).
C.3.
VerifythatUserSecurityAdministrationproceduresexisttoensurethatuniqueuserIdsareassignedtosystemusers.Incaseswheretheaccesscontrolsystempreventsindividualaccountability,compensatingcontrolsmustexist.
C.4.
Obtainasampleofaccessrequestformsfor10usersoftheapplication.Ensurethattheformsevidenceproperapprovalsfortherequestedaccess.
C.5.
Obtainacopyofthesystemgenerateduseraccessreportthatidentifiesallusersandtheirassignedauthoritylevelsanddeterminethat:
a.Onlycurrentemployeeshaveaccesstotheapplication.
b.Allusersareuniquelyidentifiedontheaccesscontrolreport.
c.Passwordsarenotdisplayedonthereport.
d.Eachuserisgrantedanaccesslevelthatiscommensuratewiththeirjobresponsibility.
e.Managementperiodicallyreviewsandapprovesuserswhohaveaccesstotheapplication.Thereviewshouldbeperformedindependentlyofthe
C.6.
ObtainacopyofthecurrentPasswordManagement/AccessControlPolicy(SeeIntranetCentral)anddeterminethatthisapplicationcomplieswithguidelinesfor:
a.Charactercomponents
b.Length
c.Passwordchangefrequency
d.Invalidpasswordattempts
e.Passwordstorage
C.7.
ObtainajobdescriptionfortheApplicationSecurityAdministratorfunction.Ensurethatthereportinglinesandresponsibilitiesforthisfunctiondonotcompromisesecuritypolicies.
C.8.
Identifytheotherresponsibilitiesassignedtodatasecurity-relatedpersonnelbesidessecurityadministration.Evaluateifaseparationofdutiesdeficiencymayexist.
C.9.
Determinewhethertherearedesignatedback-upsecurityadministrators.Ensurethattheresponsibilitiesoftheback-upsecurityadministratorsdonotcauseseparationofdutiesdeficiencies.
C.10.
Obtaincopiesofthesecurityviolationreportsandverifythattheyevidencedocumentedmanagementreview.Verifythatquestionableactivitycanbeidentifiedandisappropriatelyaddressed.
C.11.
Determinethatareviewofthesecurityadministrator’smaintenanceactivityisperiodicallyperformedbysomeoneotherthantheUser
- 配套讲稿:
如PPT文件的首页显示word图标,表示该PPT已包含配套word讲稿。双击word图标可打开word文档。
- 特殊限制:
部分文档作品中含有的国旗、国徽等图片,仅作为作品整体效果示例展示,禁止商用。设计者仅对作品中独创性部分享有著作权。
- 关 键 词:
- Application Systems IT Audit Program
 冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。
冰豆网所有资源均是用户自行上传分享,仅供网友学习交流,未经上传用户书面授权,请勿作他用。


 《雷雨》中的蘩漪人物形象分析 1.docx
《雷雨》中的蘩漪人物形象分析 1.docx
